Resource Center

Featured resources








Cloud Security Index 2023
Get Vanson Bourne research on top cloud security challenges and why Zero Trust Segmentation is an essential cloud security technology.








Gartner® Market Guide for Microsegmentation
Gartner® has named Illumio as a Representative Vendor in its 2023 Market Guide for Microsegmentation.








Forrester Study: 111% ROI Realized With Illumio Zero Trust Segmentation
Get the Forrester Total Economic Impact study of Illumio Zero Trust Segmentation. See how Illumio customers realize a 111% ROI and $10.2M in total benefits.








How Network Segmentation Helps Deliver Resilience Against NHS Cyber Threats
This report investigates the state of NHS cybersecurity and how healthcare organizations can adopt Zero Trust Segmentation (ZTS) to address current security challenges.







Ransomware Containment Explainer Video
Learn how Zero Trust Segmentation stops the spread of ransomware across your entire hybrid attack surface.







Illumio Zero Trust Segmentation Platform Explainer Video
Watch the video to learn how the Illumio Zero Trust Segmentation Platform helps you build Zero Trust, bolster cyber resilience, and achieve security ROI.








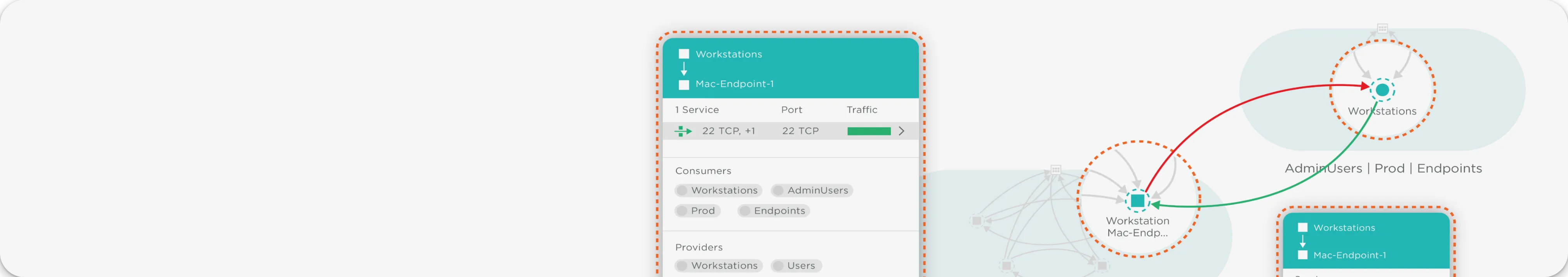
Illumio Core Explainer Video
Watch the video to learn how Illumio Core limits lateral movement and safeguards your most important data center assets.








Illumio Endpoint Explainer Video
Watch the video to learn how Illumio Endpoint delivers unparalleled visibility and proactive breach containment for your endpoints.








Cloud Workload Migration Explainer Video
Watch the video to learn how Illumio builds cyber resilience and ensures business continuity as your apps are migrated to and transformed in the cloud.








Illumio CloudSecure Explainer Video
Watch the video to learn how Illumio CloudSecure can help you confidently contain attacks in the public cloud.








Le gouvernement met en œuvre Zero Trust pour un avenir plus sûr
Webinaire du panel d'experts de FedInsider sur Zero Trust







Customer Success Advisors
Learn how Illumio Customer Success Advisors can help support your Zero Trust Segmentation deployment.








Mapping Illumio to the Department of Defense Zero Trust Reference Architecture
Learn how Illumio aligns with the architecture's seven pillars.








Cloud Security Index: Key Findings from France
Vanson Bourne summarizes research findings on the state of cloud security in French organizations.








Illumio at the Tactical Edge: Staged and Deployed Resources
Learn how Illumio delivers Zero Trust Segmentation during staging and deployment.








Illumio at the Tactical Edge: Deployed Aircraft
Learn how Illumio delivers Zero Trust Segmentation to deployed aircraft.








Illumio at the Tactical Edge: The Warfighter
Learn how Illumio delivers Zero Trust Segmentation to the warfighter.








Cloud Security Index: Key Findings from Australia
Vanson Bourne summarizes research findings on the state of cloud security in Australian organizations.








Mapping Illumio to the CISA Zero Trust Maturity Model
Learn how Illumio aligns with CISA’s five Zero Trust pillars.