See and stop lateral movement before it spreads. Experience Illumio Insights free for 14 days
Take advantage of our sandboxed environment with demo data to see how Illumio Insights lets you see and stop cyberattacks before they spread. Plus, you can add data from your cloud!
Get started in minutes. No credit card required.
- Your customer can request a trial directly
- You may request an internal evaluation from our Partner team.
- Entre em contato conosco

Thanks for signing up to trial Illumio Insights. A team member will reach out shortly with next steps. In the meantime, watch our onboarding video.

“Quando precisávamos trazer esses recursos para a Microsoft, a Illumio foi a única solução de segmentação que funcionaria na escala da Microsoft e funcionaria em nosso ambiente.”
Security Officer,
Microsoft



93% recomendam o Illumio com base em 160 avaliações validadas
Security starts with seeing the full picture
See everything
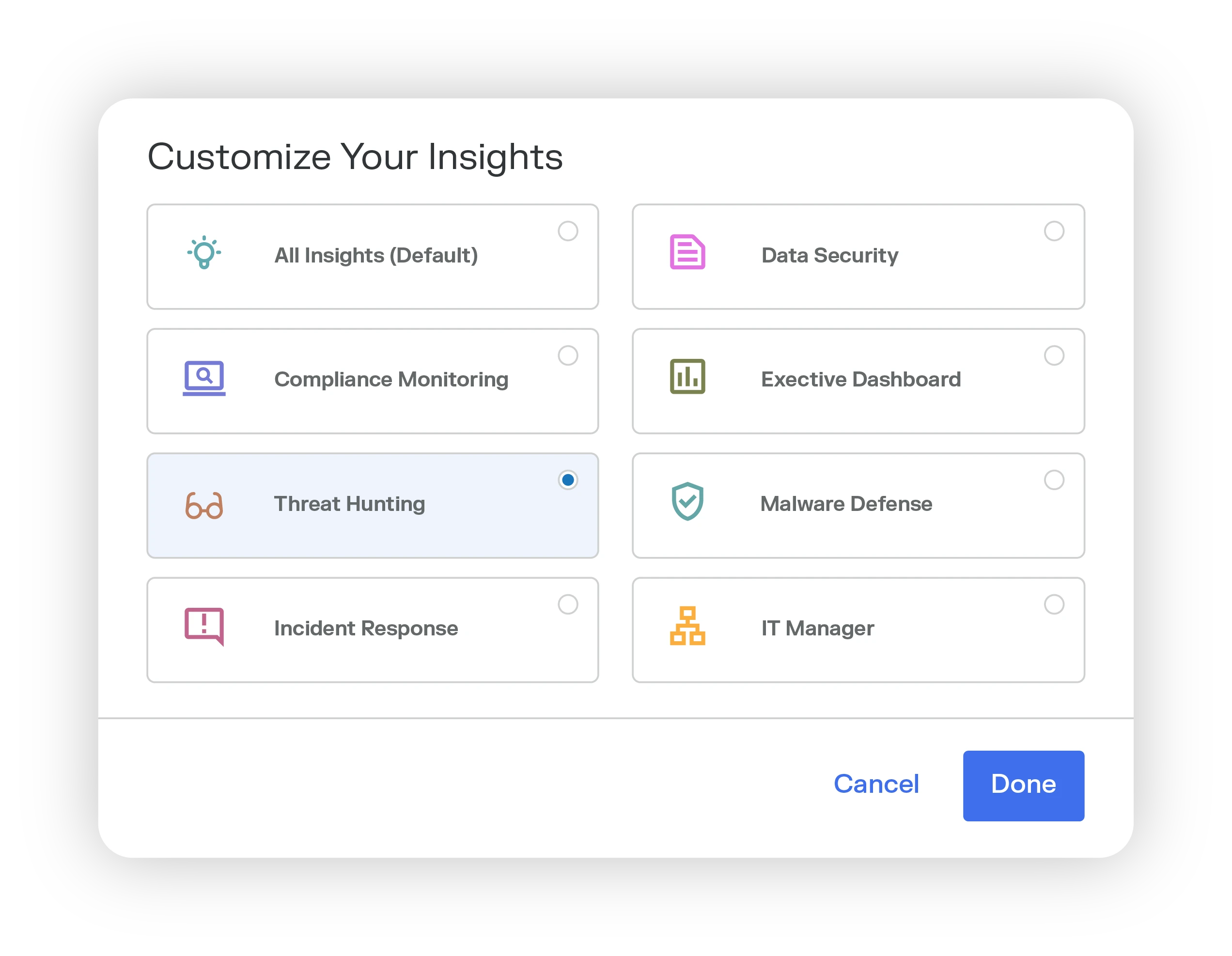
Uniform, context-rich, and scalable AI observability across hybrid, multi-cloud environments. Get a complete view of your entire hybrid, multi-cloud infrastructure.
Prioritize critical issues
Insights provides deep AI observability to identify key events, patterns, and behaviors. Reduce alert fatigue and focus on critical issues.
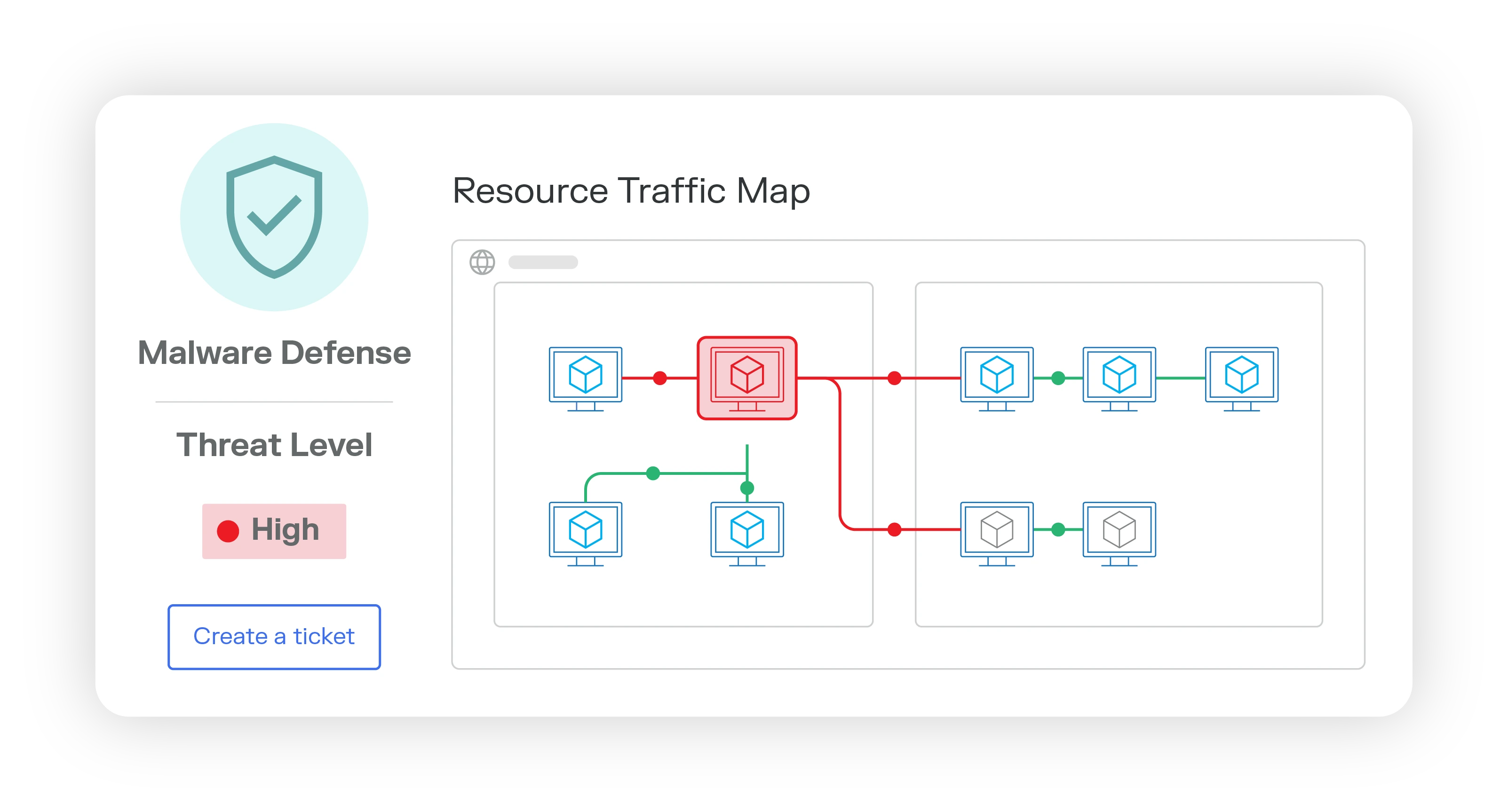
Stop attacks
Swiftly block, isolate, or segment attacks. Safeguard critical resources and minimize risk — before, during, and after an attack.