Endpoint
.svg)
Related blog posts

The Rise, Fall, and Rise Again of Peer-to-Peer-Applications
Illumio Edge secures P2P applications with enhanced visibility and by blocking unauthorized connections, preventing the lateral movement of malware.
Related resources








Illumio Endpoint Explainer Video
Watch the video to learn how Illumio Endpoint delivers unparalleled visibility and proactive breach containment for your endpoints.
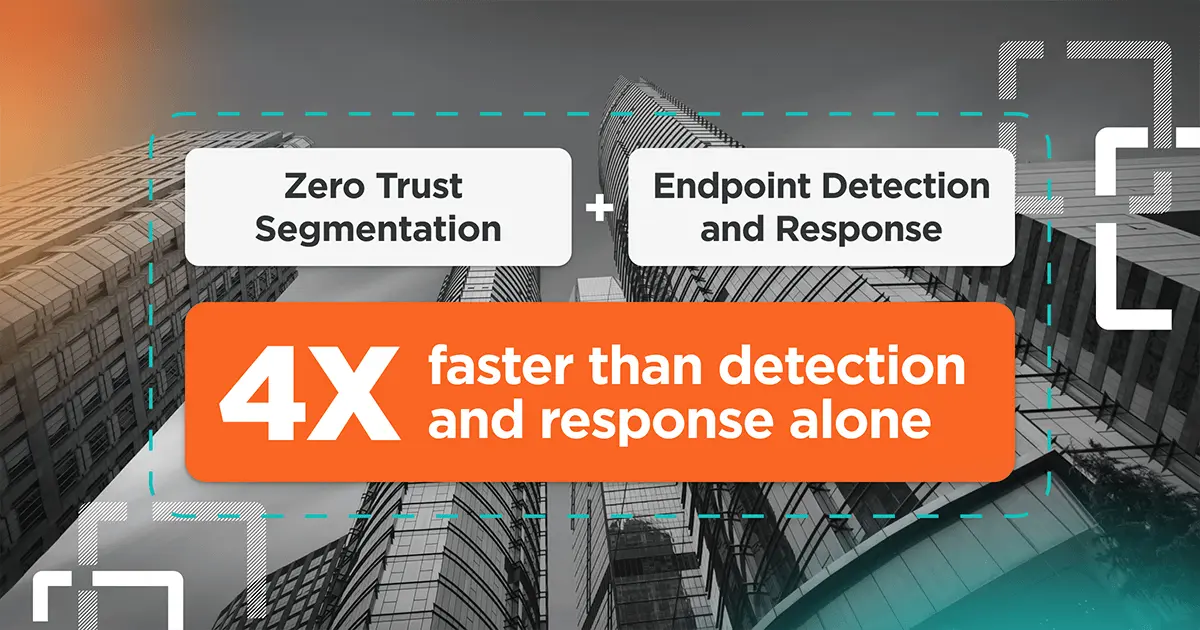







Benefits of Combining ZTS and EDR
Stop ransomware attacks nearly 4 times faster than detection and response capabilities alone.







Illumio Endpoint: Best Practices Demo
Dive into the most common use cases that can be rolled out in minutes with Illumio Endpoint, delivering Zero Trust Segmentation for end-user devices.








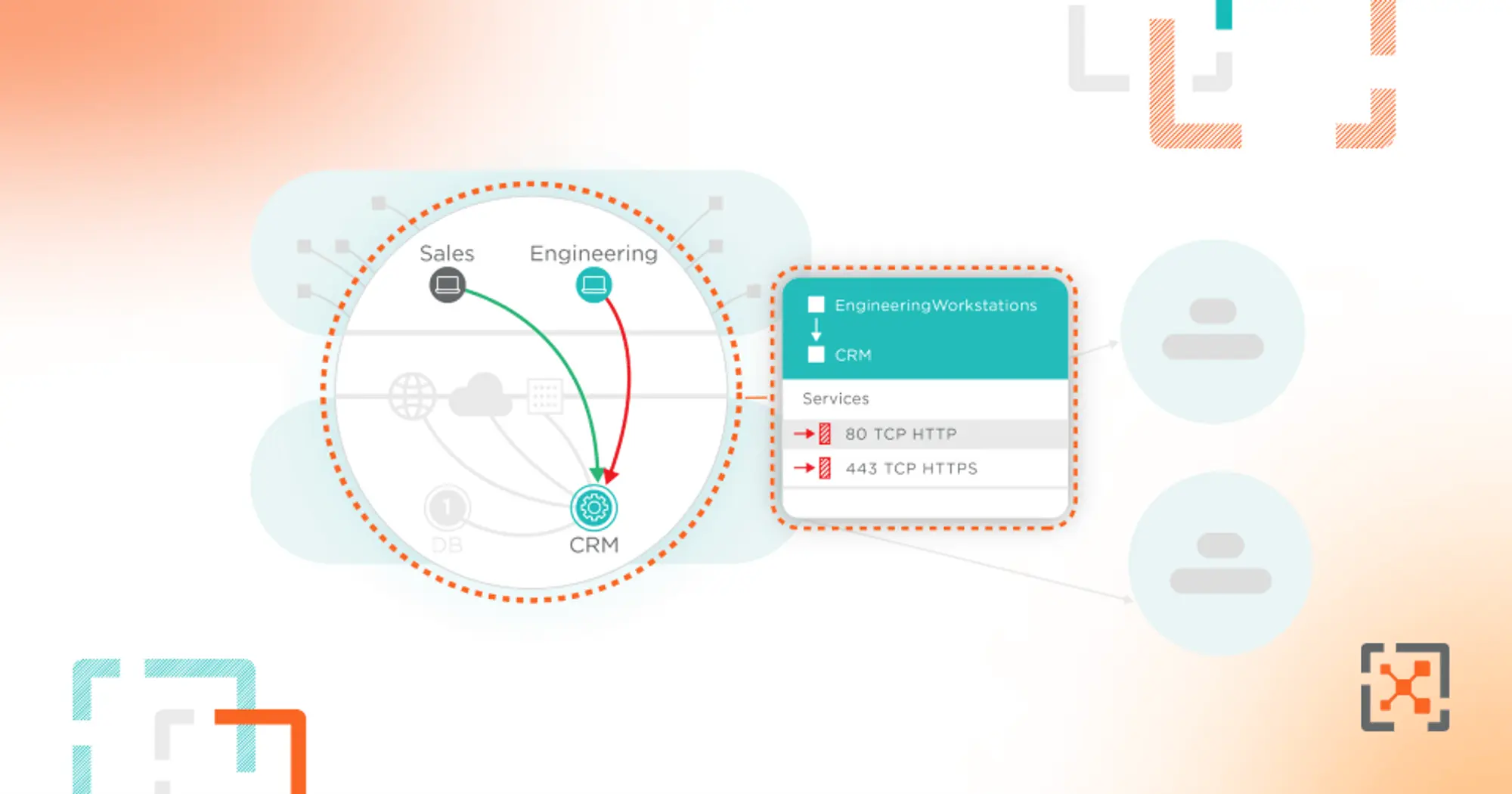
Better Together: Illumio Endpoint and EDR
Combine Illumio Endpoint breach containment and your endpoint detection and response (EDR) solution for full endpoint security.







Illumio Endpoint Overview
Illumio Endpoint brings Zero Trust Segmentation to your endpoint devices to stop the spread of inevitable cyberattacks.
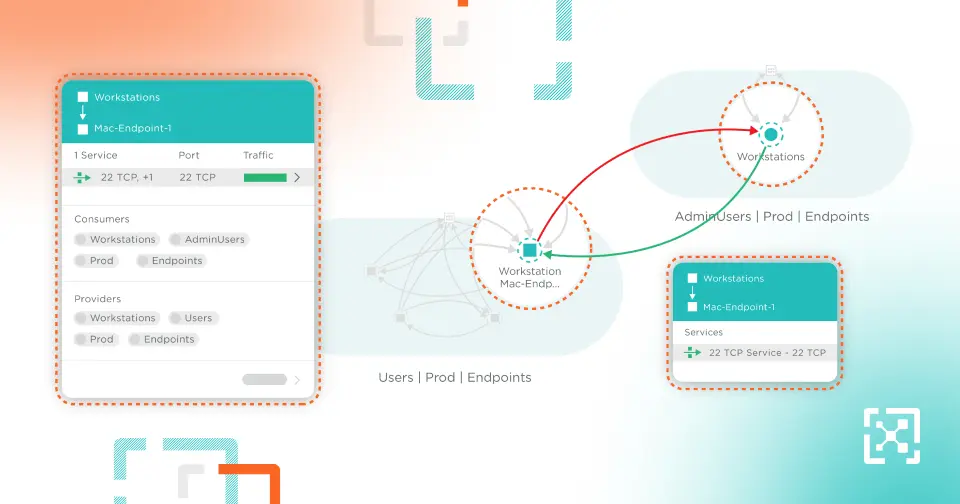







Illumio Endpoint Demo
See how Illumio Endpoint stops lateral movement and eliminates the risk that your end-user devices pose to your network.
Assume Breach.
Minimize Impact.
Increase Resilience.
Ready to learn more about Zero Trust Segmentation?
