Veja tudo, não persiga nada: as novidades do Illumio Insights
As equipes de segurança passaram anos trabalhando com visibilidade limitada.
Muitas ferramentas de segurança se concentram no perímetro da rede. Mas os atacantes modernos raramente invadem pela porta da frente. Eles se deslocam silenciosamente pelo tráfego leste-oeste, saltando de sistema em sistema até alcançarem ativos críticos.
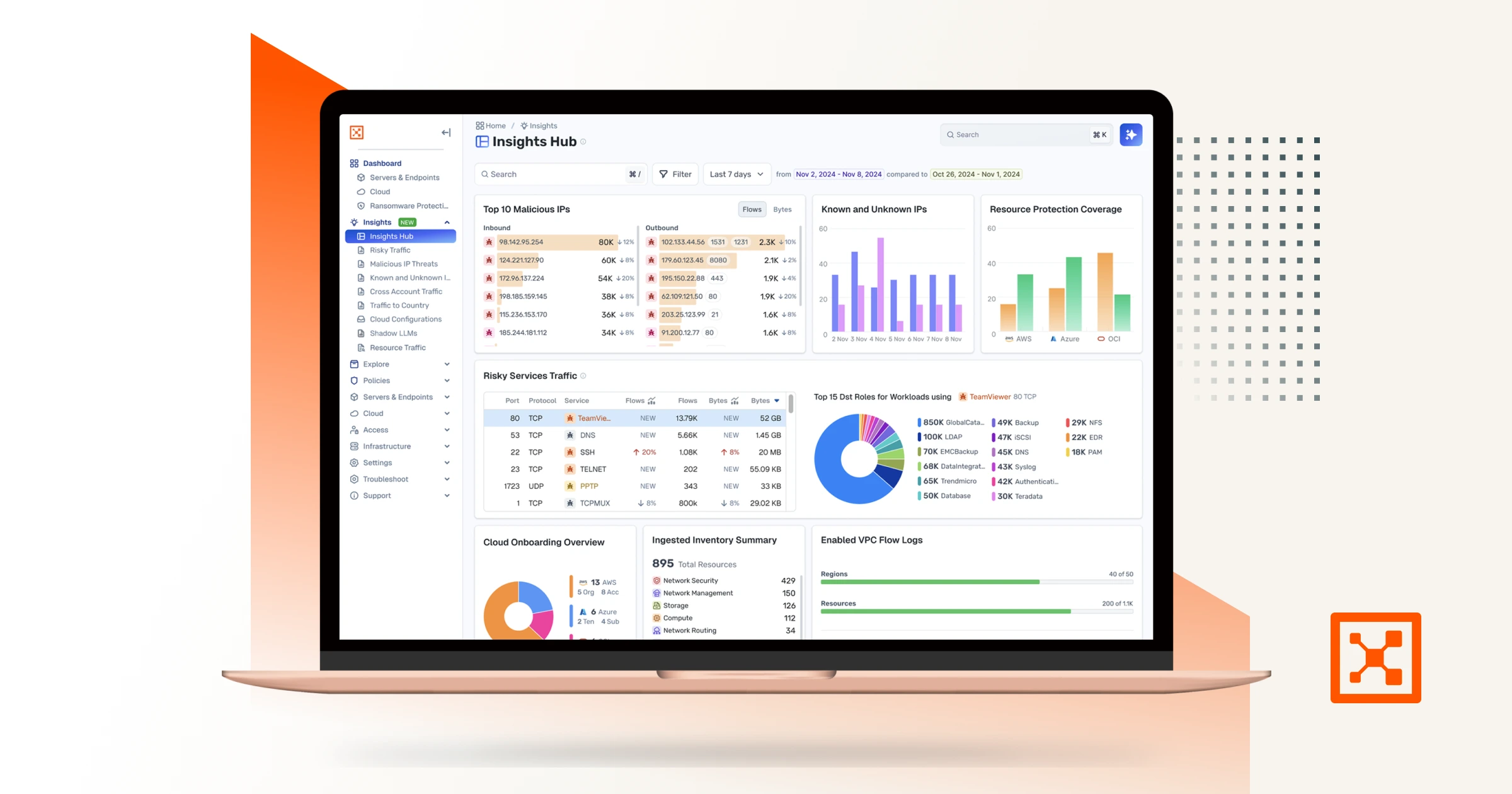
O Illumio Insights foi desenvolvido para resolver esse problema. Isso ajuda as equipes de segurança a ver como o tráfego se move em seus ambientes. Com a versão mais recente, a plataforma torna-se ainda mais útil para as equipes que dependem dela diariamente.
Esta atualização introduz três melhorias principais:
- O VEN Insights oferece uma visibilidade mais profunda do tráfego dentro de data centers privados.
- As regras de tráfego filtram o ruído para que os analistas possam se concentrar na atividade que realmente importa.
- O Label Insights adiciona um contexto comercial claro às investigações de ameaças.
Em conjunto, essas capacidades ajudam os defensores a se concentrarem em ameaças reais. As equipes de segurança dedicam menos tempo à análise de dados e mais tempo à prevenção de ataques.
VEN Insights: iluminando seu data center privado
Para organizações que executam cargas de trabalho localmente, o tráfego leste-oeste tem sido, há muito tempo, uma das áreas mais difíceis de monitorar.
Os registros do firewall mostram o que atravessa o perímetro da rede. Mas raramente mostram como os sistemas se comunicam dentro do ambiente. Esse tráfego interno é exatamente o que os atacantes usam para se movimentar lateralmente, escalar privilégios e alcançar sistemas críticos.
A VEN Insights preenche essa lacuna ao estender a telemetria de fluxo do Illumio Insights para o data center privado.
Ele ingere dados de nós de aplicação virtuais (VENs) da Illumio e os correlaciona com os fluxos do firewall. Isso proporciona às equipes de segurança a mesma visibilidade abrangente dos ambientes locais que elas esperam na nuvem.
Com o VEN Insights, os analistas podem analisar padrões de tráfego de rede usando fluxos de VENs e firewalls para obter visibilidade completa.
As equipes de segurança podem descobrir atividades no sentido leste-oeste que estavam anteriormente ocultas. Por exemplo, os sistemas de produção podem estar se comunicando com ambientes que não são de produção de maneiras que violam as políticas. Ativos críticos podem receber conexões de entrada inesperadas. Serviços de alto risco podem estar sendo executados dentro do centro de dados sem o devido conhecimento.
Em vez de depender de registros de firewall que mostram apenas parte da história, o VEN Insights fornece uma visão completa do tráfego interno. Isso também acrescenta o contexto necessário para entender por que os padrões de comunicação são importantes.
Para equipes de operações de segurança que têm dificuldade em conectar a atividade local com a telemetria na nuvem, o VEN Insights cria uma visão unificada do ambiente. Isso torna muito mais fácil detectar comportamentos de risco e investigar possíveis movimentos laterais.
Regras de trânsito: sinal alto, ruído baixo
Todas as plataformas de segurança coletam grandes quantidades de dados de fluxo de rede. O desafio não é coletar os dados, mas sim focar no que importa.
Sem uma maneira clara de filtrar os sinais do ruído, os analistas podem facilmente ficar sobrecarregados.
As Regras de Tráfego do Insights resolvem esse problema, dando às equipes de segurança controle sobre quais fluxos aparecem em suas análises e quais são ocultos.
Por exemplo, as equipes podem direcionar o tráfego de entrada para balanceadores de carga e gateways de tradução de endereços de rede (NAT). Eles podem excluir fluxos de norte a sul para manter as investigações focadas no movimento lateral leste-oeste. Eles também podem filtrar tráfego sintético, varreduras ou fluxos de testes de penetração, para que o Insights destaque apenas a atividade real.
Essa clareza tem um impacto direto nas operações de segurança.
Quando os analistas confiam nos dados que têm em mãos, eles trabalham mais rápido. Eles passam menos tempo se perguntando se os alertas são falsos positivos e mais tempo investigando ameaças reais.
As regras de tráfego dão às equipes de segurança controle sobre o formato de seus dados, e não apenas sobre o acesso a eles. As investigações tornam-se mais focadas. As escaladas tornam-se mais confiantes. Os tempos de resposta melhoraram.
Quando combinado com a pontuação de ameaças baseada em IA do Insights, esse sinal mais claro ajuda as equipes de segurança a passar da detecção à contenção muito mais rapidamente.
Análises de rótulos: o contexto é tudo
Os endereços IP brutos e os números de porta mostram para onde o tráfego é direcionado. Mas eles não mostram se a atividade é relevante.
A Label Insights preenche essa lacuna adicionando detalhes comerciais à atividade de rede em ambientes híbridos. Isso integra informações como níveis de ambiente, proprietários de aplicativos, escopo de conformidade e localização diretamente na visualização da investigação.
Quando um analista observa um pico de tráfego entre duas cargas de trabalho, o Label Insights exibe os rótulos que descrevem esses sistemas em termos comerciais claros. Por exemplo, pode mostrar um ambiente de Staging comunicando-se com um ambiente de Produção, sistemas PCI conectando-se a aplicativos de Varejo ou um sistema de Marketing usando RDP.
Este contexto transforma uma anomalia básica de rede em uma questão de segurança clara.
Os analistas podem visualizar rapidamente o possível raio de impacto e compreender o efeito sobre a conformidade. Eles também podem explicar o que está acontecendo aos líderes empresariais sem precisar consultar bancos de dados de ativos ou outros documentos.
Por que essas atualizações são importantes agora?
Os ataques modernos são rápidos. Uma vez que um invasor conquista uma posição inicial, raramente para em apenas um sistema.
Eles se movem lateralmente, buscando os recursos que mais importam. Quanto mais tempo esse movimento permanecer invisível, maior se tornará a brecha.
As equipes de segurança não podem se dar ao luxo de ter pontos cegos em seus ambientes. Eles precisam de visibilidade clara sobre como os sistemas se comunicam, sinais fortes em seus dados e um contexto de negócios que explique por que a atividade é importante.
É exatamente isso que essas atualizações do Insights oferecem.
A VEN Insights proporciona visibilidade aos centros de dados privados, onde a movimentação leste-oeste tem sido difícil de observar por muito tempo. As regras de trânsito eliminam o ruído para que os analistas possam se concentrar na atividade real. O Label Insights adiciona o contexto de negócios necessário para entender o risco e agir com confiança.
Em conjunto, essas funcionalidades ajudam as equipes de segurança a passar mais rapidamente da detecção à ação. Em vez de perseguir alertas e adivinhar o impacto, os analistas podem visualizar o ambiente com clareza e responder com precisão.
Em operações de segurança modernas, clareza é sinônimo de velocidade. E a velocidade é o que impede os ataques antes que se espalhem.
Pronto para enxergar seu ambiente com clareza? Experimente o Illumio Insights gratuitamente. Para proporcionar visibilidade híbrida completa às suas equipes de rede e segurança.

.webp)




