.png)

神話に関するファクトシート
Anthropic社のClaude Mythos Previewは、ゼロデイ脆弱性を機械の速度で発見し、兵器化しました。侵入封じ込めが現在唯一有効な防御策となっている理由を以下に説明します。
2026年初頭、Anthropic社のClaude Mythos Preview AIモデルは、主要なオペレーティングシステム、ブラウザ、コアインフラストラクチャ全体にわたって、数千もの重大なゼロデイ脆弱性を自律的に発見し、その多くに対して動作するエクスプロイトを構築した。脆弱性の発見から実際の悪用までの時間は、ほぼゼロにまで短縮された。
それは、あらゆるセキュリティプログラムの前提となっている時間的な制約を覆すものだ。30日から90日というパッチサイクルでは、数秒単位で動き回る攻撃者のスピードには追いつけない。検出作業は依然として人間の速度で行われる。昔からある疑問――「攻撃者が悪用する前に、パッチを適用できるだろうか?」—もはや有用な回答ではない。新たな問題は、攻撃者が一度侵入した後、どれだけ遠くまで移動できるかということだ。
学習内容:
- ポスト・ミトスの世界では、パッチサイクルと予防優先モデルが拡張性に欠ける理由
- ID駆動型でマルウェアを使用しない攻撃が、シグネチャベースの検出を回避する方法
- なぜ今や、探知速度ではなく爆発半径がセキュリティの有効性を決定づけるのか?
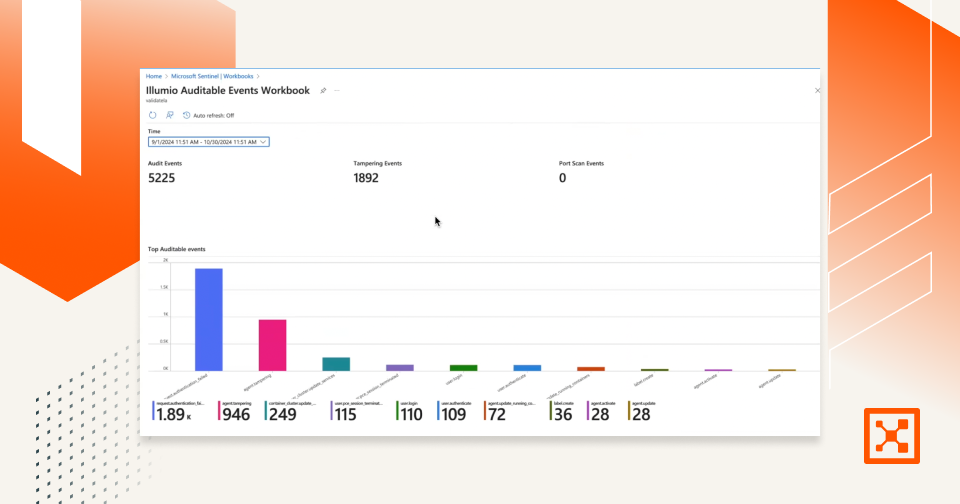
- Illumio Segmentationは、攻撃者がどんな脆弱性を悪用しようとも、横方向の動きをどのように抑制するのか。
ハイライト
主な利点
アセットのプレビュー
2026年初頭、Anthropic社のClaude Mythos Preview AIモデルは、主要なオペレーティングシステム、ブラウザ、および広く使用されているインフラストラクチャ全体にわたって、数千もの重大なゼロデイ脆弱性を自律的に発見し、その多くに対して動作するエクスプロイトを作成しました。Firefoxだけでも、発見された脆弱性の72%以上が実際に動作するエクスプロイトに変換された。
これは研究のベンチマークではありません。それは、世界中のサーバー、ブラウザ、ファイアウォールを動かす本番環境のコードに対して実行された。多くは数十年にわたって配備されていたが、誰もその欠陥に気づかなかった。
数週間かけて準備する守備側は、秒単位で動く攻撃側にはついていけない。






違反を想定します。
影響を最小限に抑えます。
レジリエンスを高めます。
予期しないことがいつでも発生する可能性があるという前提から始めると、次の動作が促進されます