Wie Illumio + Armis moderne OT-Umgebungen sichern
Unternehmen haben Jahrzehnte damit verbracht, in die Cybersicherheit zu investieren.
Warum berichten 58 % der Organisationen, die im letzten Jahr von einem Cyberangriff betroffen waren, immer noch, dass sie ihren Betrieb einstellen mussten?
Und warum führen diese Angriffe dazu, dass 40 % der Unternehmen einen erheblichen Umsatzverlust erleiden und 35 % einen Markenschaden erleiden?
Insbesondere für Operational Technology (OT)-Teams stellen diese Statistiken eine existenzielle Bedrohung dar.
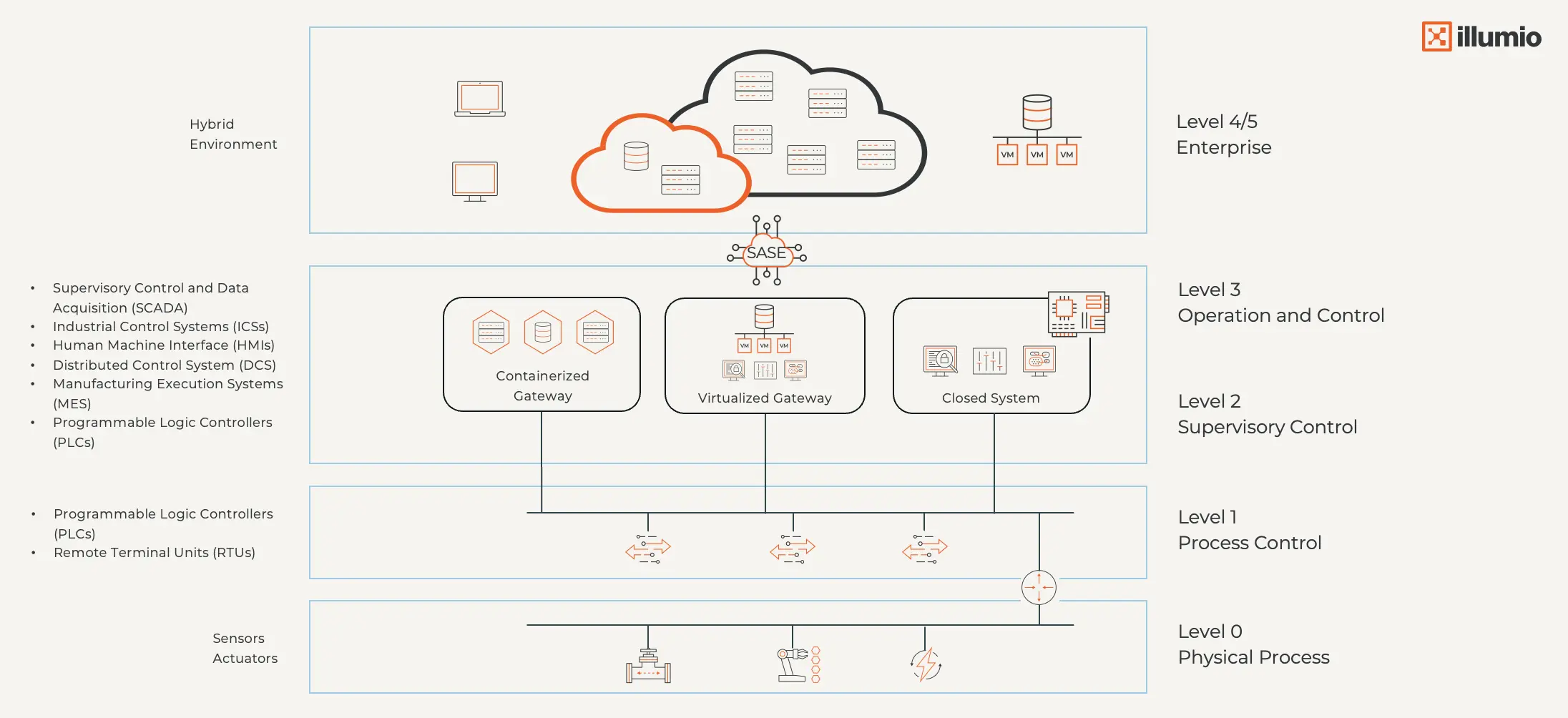
Jahrzehntelang waren Fabriken, Versorgungsunternehmen und kritische Infrastrukturen auf Air-Gap-Netzwerke und Perimetersicherheit angewiesen. Da die digitale Transformation jedoch die Konvergenz von IT und OT vorantreibt, sind diese Strategien nicht mehr haltbar.
Ältere Industriesysteme koexistieren jetzt mit Cloud-Plattformen, IoT-Sensoren und virtualisierten Gateways. Das Ergebnis ist eine Angriffsfläche, die weit aufgerissen wird.
Die gemeinsame Lösung von Illumio und Armis kann Ihnen helfen, die Sicherheitslücke zu schließen.
Das Zero-Trust-Mandat für OT-Sicherheit
Die Absicherung moderner OT-Systeme ist nicht einfach. Heutige Sicherheitsteams sind gezwungen:
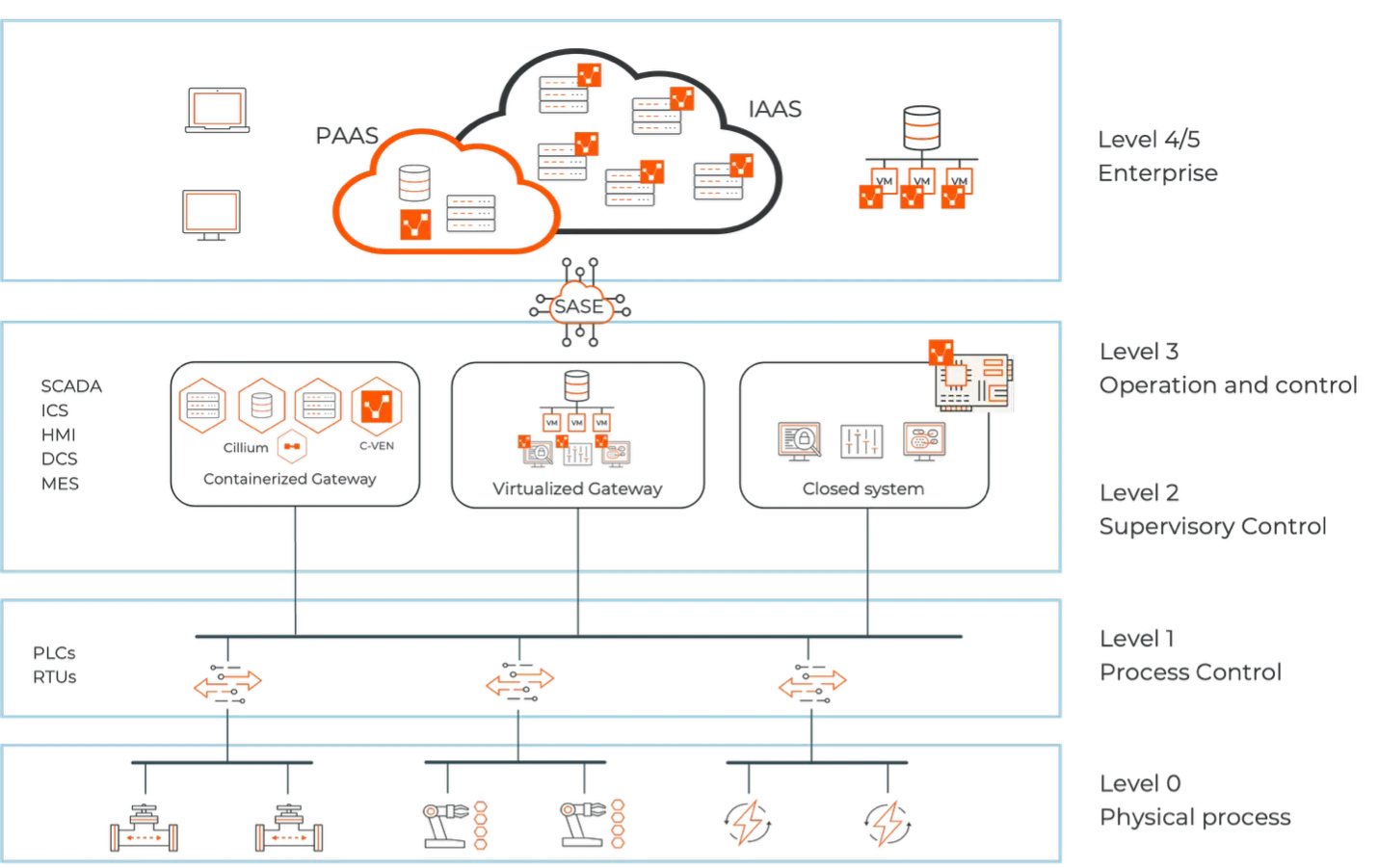
- Migration von Air-Gapped- zu Hybrid-Umgebungen
- Einführung von containerisierten Gateways und SASE-Architekturen
- Verwalten von IaaS- und PaaS-Integrationen
Aber diese Modernisierung übersteigt oft die Investitionen in die Sicherheit, was zu einem gefährlichen "Defizit bei der Sicherheitstransformation" führt.
Das alte Purdue-Modell funktionierte, als industrielle Systeme isoliert waren.

Aber in einer Welt von containerisierten Gateways, hybriden Umgebungen und virtualisierter OT fallen statische Perimeter auseinander. Das Purdue-Modell wurde seitdem aktualisiert, um die moderne Komplexität widerzuspiegeln.
Eine Zero-Trust-Strategie für OT-Umgebungen ist der einzige Weg in die Zukunft. Es validiert kontinuierlich jeden Benutzer, jedes Gerät und jede Arbeitslast, beschränkt den Zugriff auf das Notwendigste und passt die Richtlinien automatisch an veränderte Umgebungen und Risiken an.
Illumio + Armis: ein praktischer Weg zu Zero Trust in der OT
Armis und Illumio definieren neu, wie Zero Trust in komplexen industriellen Umgebungen aussieht.
Zusammen kombinieren sie eine umfassende Asset-Transparenz mit Echtzeit-Segmentierung und -Durchsetzung, ohne den Betrieb zu unterbrechen.
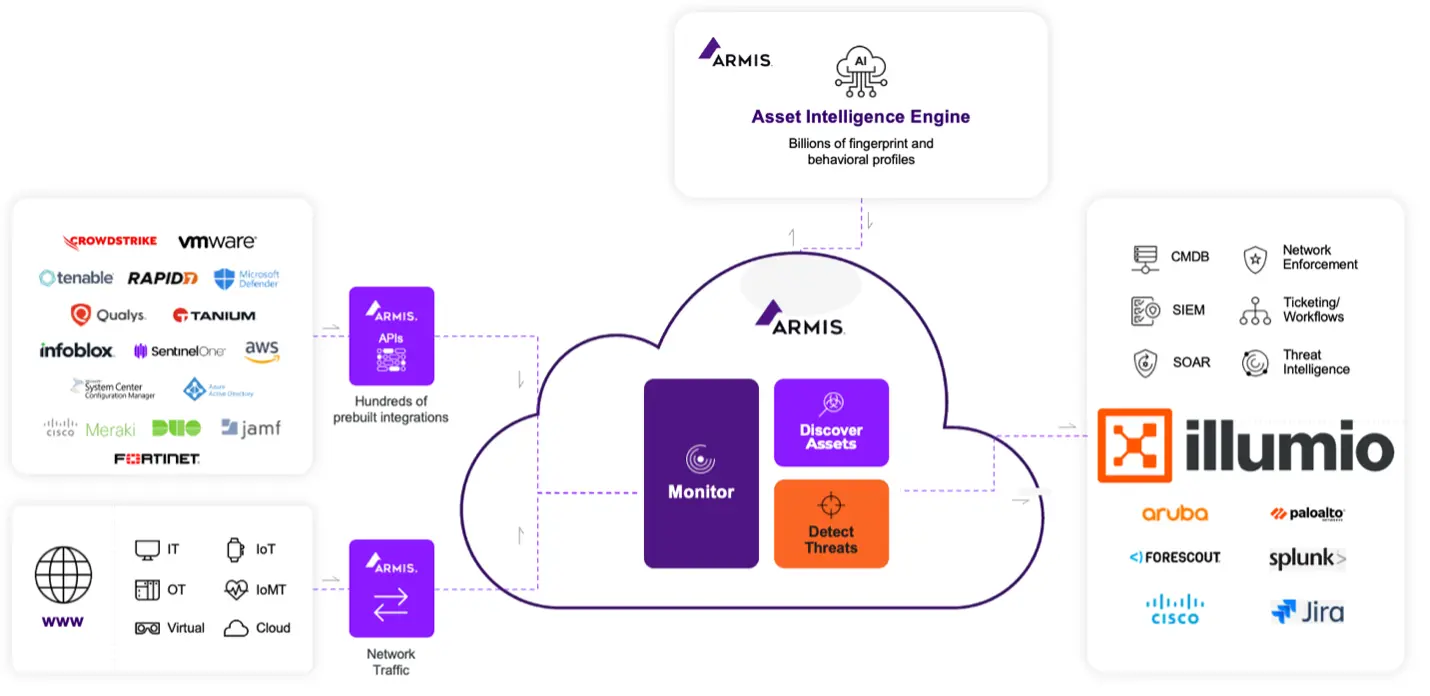
Armis: Sehen und verstehen Sie Ihre IT, OT und IoT
Armis bietet umfassende Transparenz über IT, OT und IoT hinweg.
Die passive Überwachung deckt Gerätetyp und -rolle, Netzwerkverhalten und Kommunikationsmuster, die Platzierung innerhalb des Purdue-Modells sowie den Risiko- und Schwachstellenkontext auf.
Diese Intelligenz ist die Grundlage für Segmentierung und Schutz.
Armis überwacht passiv jedes angeschlossene Gerät in IT, OT und IoT und bietet einen unübertroffenen Einblick in:
- Gerätetyp und -rolle
- Netzwerkverhalten und Kommunikationsmuster
- Layer-Platzierung innerhalb des Purdue-Modells
- Risiko- und Vulnerabilitätskontext
Dieser Kontext ist für die Segmentierung und den Schutz kritischer OT-Assets unerlässlich.
Illumio: Segmentierung ohne Risiko durchsetzen
Illumio nutzt die Erkenntnisse von Armis und wendet adaptive, risikoinformierte Segmentierungsrichtlinien an.
Dazu gehören:
- Segmentierung mit dem Purdue-Modell im Hinterkopf: Sperren Sie den Datenverkehr zwischen SCADA, DCS, MES und ERP, sodass jedes System nur das spricht, was es soll.
- Dynamische Reaktion auf Bedrohungen: Wenn Armis etwas Verdächtiges entdeckt, reagiert Illumio sofort, unterbricht den Zugang oder isoliert Geräte, bevor sich Bedrohungen ausbreiten.
- Agentenlose Steuerung: Schützen Sie empfindliche ICS- und SPS-Geräte, ohne sie zu berühren. Die Illumio VEN/NEN-Architektur setzt Richtlinien sicher durch, ohne dass Agenten erforderlich sind.
Dieser Ansatz ist sicher, einfach zu skalieren und sorgt dafür, dass Ihr Betrieb auch bei einem aktiven Angriff widerstandsfähig bleibt – selbst in den strengsten regulierten Umgebungen.
Die wichtigsten Vorteile der Integration von Illumio + Armis
Die gemeinsame Lösung von Illumio und Armis wurde für die täglichen Herausforderungen entwickelt, mit denen OT- und Sicherheitsteams konfrontiert sind.
Keine Unterbrechung des Betriebs
Die meisten Sicherheitstools verlangsamen Sie mit Agenten oder umfangreichen Netzwerkänderungen. Doch Illumio und Armis gehen einen anderen Weg.
Eine schlanke Architektur schützt kritische Systeme, ohne empfindliche Geräte wie SPS, RTUs oder SCADA-Controller zu berühren.
Illumio setzt Richtlinien über sein VEN/NEN-Modell durch, während Armis passive, agentenlose Transparenz bietet, sodass Sie alles sehen und sicher bleiben, ohne zusätzliche Risiken einzugehen.
Closed-Loop-Verteidigung, die sich in Echtzeit anpasst
Erkennung und Durchsetzung können nicht in Silos funktionieren. Sie füttern sich gegenseitig.
Wenn Armis etwas Verdächtiges entdeckt, wie z. B. eine seltsame Protokollaktivität oder ein Gerät, das eine öffentliche IP-Adresse anpingt, reagiert Illumio sofort, indem es es sperrt oder den Zugriff verschärft. Das Ergebnis sind schnellere Reaktionen, eine kürzere Verweilzeit und ein kleinerer Strahlradius, ohne auf manuelle Eingriffe warten zu müssen.
Compliance-freundliche Transparenz und Audit-Trails
In stark regulierten Branchen bedeutet Transparenz in Ihren hybriden Umgebungen das Überleben.
Die Integration von Illumio + Armis bietet auditbereite Protokolle, Richtliniensimulationen und Vorab-Änderungen, damit Teams Aktualisierungen mit Zuversicht vornehmen können.
Unabhängig davon, ob Sie sich an NIST, IEC 62443 oder ISO 27001 ausrichten, macht diese gemeinsame Lösung die Einhaltung von Vorschriften klarer, schneller und einfacher, ohne den Betrieb zu verlangsamen.
Einheitliche Sicherheit mit echtem Geschäftswert
Gemeinsam liefern Illumio und Armis Ergebnisse, die am wichtigsten sind: stärkere Abwehrmechanismen, reibungslosere Audits und sicherere Modernisierung.
Sie unterbinden die seitliche Ausbreitung , bevor sie sich ausbreiten kann, stoppen Ransomware an der Quelle und vereinfachen die Einhaltung der Vorschriften durch klare, überprüfbare Kontrollen.
Und wenn sich Ihre OT-Umgebung weiterentwickelt, egal ob es sich um SASE, virtualisierte Gateways oder Hybrid Cloud handelt, passt sich die Lösung an. Dies stellt sicher, dass Sie Ausfallsicherheit gewinnen, ohne an Transparenz oder Betriebszeit zu verlieren.
Sie müssen sich nicht zwischen Fortschritt und Schutz entscheiden. Mit Illumio und Armis können Sie sicher modernisieren, da Sie wissen, dass Ihre wichtigsten Systeme stets sicher sind.
Schließung der Lücke bei der OT-Transformation
Cyberangriffe werden nicht langsamer, und OT-Umgebungen werden immer komplexer.
Veraltete Abwehrmaßnahmen – Air Gaps, statische Perimeter und isolierte Tools – können einfach nicht Schritt halten. Jede Verzögerung bei der Schließung des "Sicherheitstransformationsdefizits" macht kritische Infrastrukturen anfällig für Ransomware, Ausfallzeiten und regulatorische Risiken.
Deshalb ist die Integration von Illumio + Armis jetzt wichtiger denn je.
Durch die Kombination von umfassender Asset-Transparenz mit Echtzeit-Segmentierung und -Durchsetzung bietet es Zero-Trust-Sicherheit, die produktionsbereit, Compliance-freundlich und für die Realitäten der modernen OT konzipiert ist.
Sie können nicht auf den nächsten Vorfall warten, um eine Änderung zu erzwingen. Mit Illumio und Armis können Sie noch heute Resilienz aufbauen, damit Ihr Unternehmen ohne Angst vor Unterbrechungen innovativ sein, modernisieren und wachsen kann.


.webp)




