Cybersecurity
Cybersecurity is a term that defines the processes, technologies, and practices used to safeguard devices, applications, networks, and data from damage or unauthorized access. Cybersecurity is also known as electronic information security or information technology security.
Why is cybersecurity important?
Today, almost everything relies on computers and the Internet. Communications, entertainment, transportation, shopping, medical systems, and government systems all require accurate data that is available when it is needed. Much of this data is sensitive, like personally identifiable information (PII), protected health information (PHI), and financial details.
The effects of cyberattacks are not limited to the theft of information and the destruction of people's lives. Attacks can damage businesses through fines, data loss, system damage, and loss of reputation.
Threats to these systems and data increase every day, as cybercriminals become more sophisticated. The bar to successfully committing cyber theft and getting away with it is pretty low. Hackers can automate their crimes and launch attacks on multiple targets at once. A successful cybersecurity program will have these attackers looking elsewhere because hackers mainly look for easy opportunities.
What are the different types of cybersecurity?
There are different types of cybersecurity, and it helps to categorize cybersecurity under a few topics to help organizations and people protect themselves.
Critical infrastructure security
Much of the electricity grid is accessible via the Internet, and some of the systems required for the operation of a business will be. Systems included in critical infrastructure include the electricity grid, water purification systems, traffic systems, and hospitals. Critical infrastructure security protects systems where attacks can bring modern societies to a halt.
Application security
Application security involves protecting specific applications from attack. Validating input before an application can process it can prevent buffer overflows, SQL injection, denial of service attacks, cross-site scripting, and other types of cyberattacks. Using secure authentication processes also prevents hacking attempts.
Network security
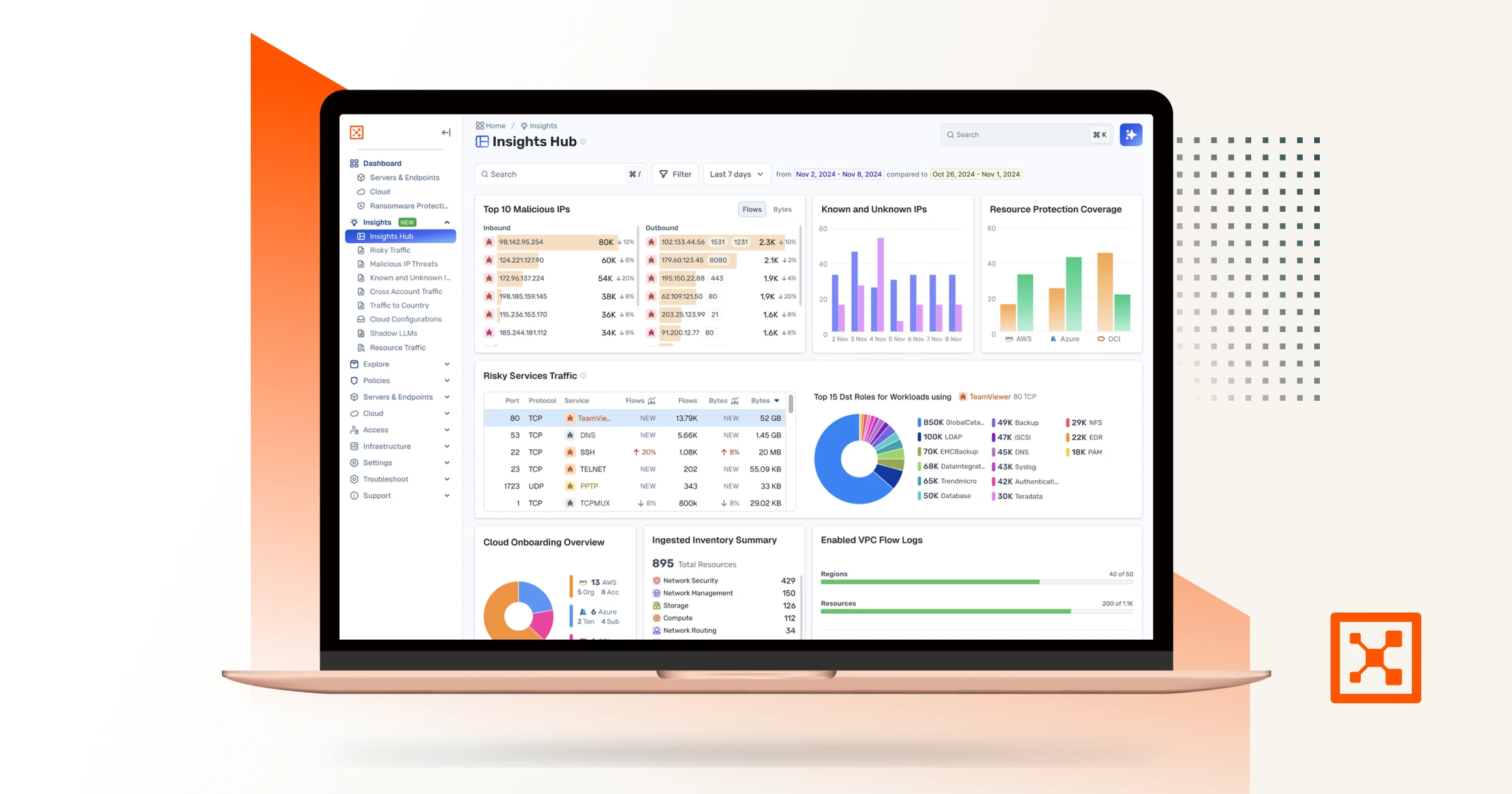
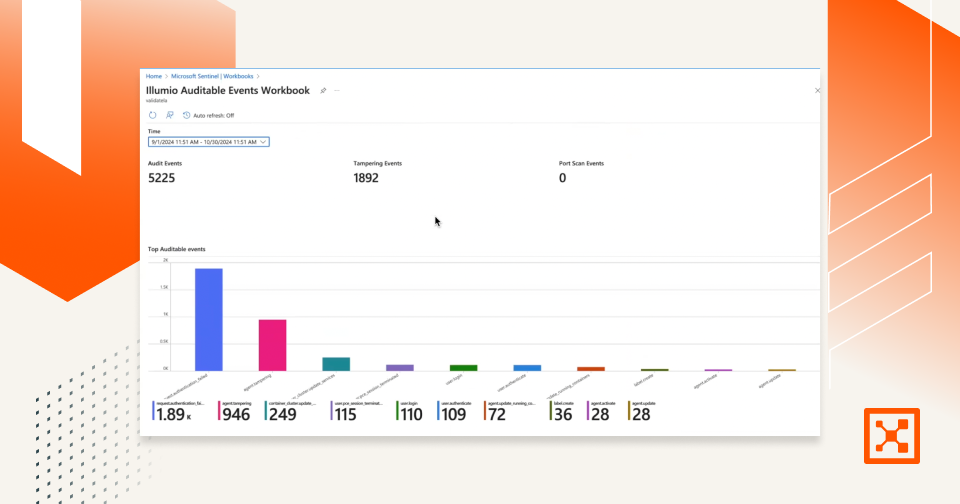
Network security protects a corporate network from attacks that result from the Internet. To be connected to the rest of the business world, your network needs to be connected to the Internet and that puts it at risk. Network security technologies include firewalls to filter and block malicious connections, intrusion prevention systems that detect and prevent identified threats, and segmentation, which prevents the spread of breaches across a network.
Endpoint security
The traditional version of endpoint security is antivirus and anti-malware. These tools detect malicious software based on signatures of known threats and then either remove the threat or quarantines it until it can be dealt with. Endpoint security evolved to include features like personal firewalls, host intrusion prevention, and host encryption. Recent developments in endpoint security include next-generation antivirus and endpoint segmentation tools that can prevent localized attacks from moving across a network.
What are the challenges of cybersecurity?
New varieties of cyberattacks show up every day, but there are a few general categories of threats that a cybersecurity team must face every day. Here are some of those challenges.
Phishing attacks
Phishing attacks usually happen via email and are an attempt to trick someone into entering their credentials into a fraudulent website. The attacker can steal personal login credentials, credit card details, or corporate login details.
Ransomware
Ransomware is malicious software that can block access to files, data, or computer systems until a ransom, usually as cryptocurrency, is paid to the attackers. But there is no guarantee that access will be returned.
Malware
Malware is a very general term that applies to any type of software that can damage a system, applications, or data. This can include viruses, worms, spyware, adware, trojans, and other malicious software. Malware can infect a device and then use network connections to infect an entire network if it doesn't have the proper security.
Top 10 cybersecurity best practices
Having a powerful set of cybersecurity policies and procedures in place can save an enterprise the hassle and cost involved in dealing with a data breach or other type of cyber attack. Here are a few best practices of cybersecurity:
- Regularly back up data to prevent data loss if an attack happens
- Install anti-virus software to stop known threats
- Use multi-factor authentication for an extra layer of security in case of credential theft
- Enforce a password policy to ensure strong passwords
- Audit users and groups to ensure that users have access to only the data and applications they need to get their work done
- Use a firewall to provide basic perimeter security of your network
- Train employees on security threats so they are less vulnerable to phishing attacks and other hacking attempts that depend on social engineering
- Connect to secure Wi-Fi
- Use segmentation to break your network into multiple domains to prevent the lateral movement of any threat
- Align with your IT department to help support information security protocols and employee training
When a corporate network is connected to the Internet, it is vulnerable to attack. However, if you are prepared and implement good security practices, you can prevent most cyberattacks before they happen.
Learn more
See how the Illumio Zero Trust Segmentation Platform aligns with your top cybersecurity initiatives, from Zero Trust and cloud security to cyber resilience.
.png)
%20(1).webp)
.webp)
.webp)

.webp)