Meet every compliance mandate with visibility, resilience, and speed
Compliance isn’t optional, but it doesn’t have to be painful. From GDPR and HIPAA to PCI DSS and DORA, Illumio delivers the visibility, control, and resilience you need — and regulators demand.
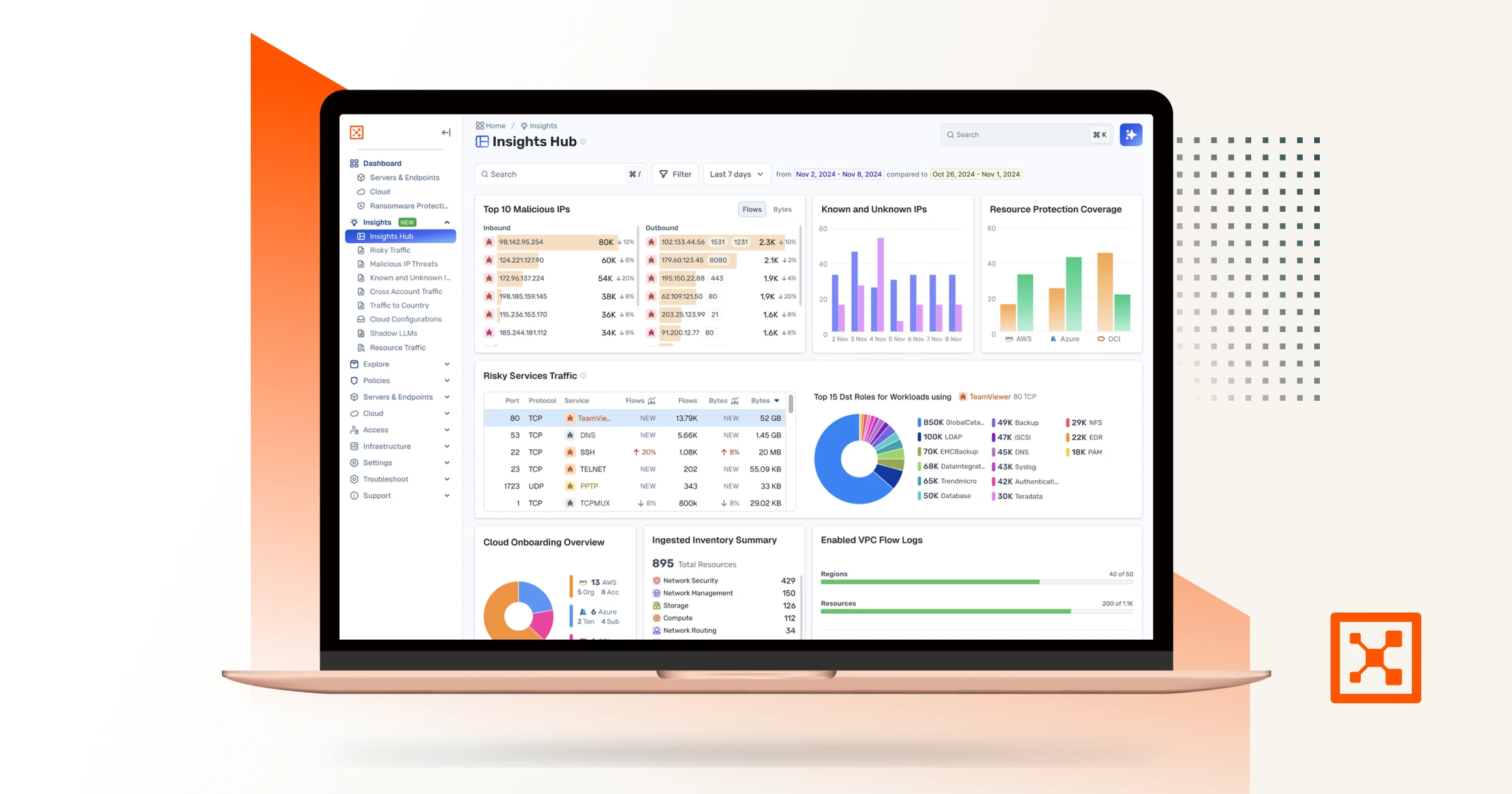
Explore Illumio Insights




Noncompliance will cost you
$10.22M
The U.S. average breach cost hit $10.22 million in 2024, driven largely by higher regulatory fines.
32%
Nearly one-third of breached organizations paid a regulatory fine.
>$100,000
Almost half of fines against breached organizations exceeded $100,000.

Illumio makes security compliance simple
Protect your critical applications, assets, and sensitive data. Simplify your security and compliance. Build true cyber and operational resilience with Illumio — the world leader in breach containment.

Frankfurter Volksbank invests in Illumio for compliance success
.svg)
.avif)
Explore Illumio Insights free
See how AI-powered observability helps you detect, understand, and contain threats faster.





.webp)