Your biggest attack surface is the one your tools aren't watching.
Lateral movement is how breaches become disasters. Illumio stops the spread at the first workload — no network redesigns, no downtime, no risky pathways.

Welcome to the Post-Breach Era
In a Ponemon study, 44% of organizations said they can’t quickly identify or contain attacks.
Ransomware attacks compromised critical systems is a quarter of all ransomware attacks.
Just 13% of organizations hit by ransomware recovered all of data affected in the attack.
In the age of agentic AI, breaches are the new normal.
Stopping AI-fueled attacks requires three things most tools don't provide: visibility into east-west traffic, policy enforced at the workload, and audit-ready proof.
Here’s how Illumio helps you contain the breach for resilience:
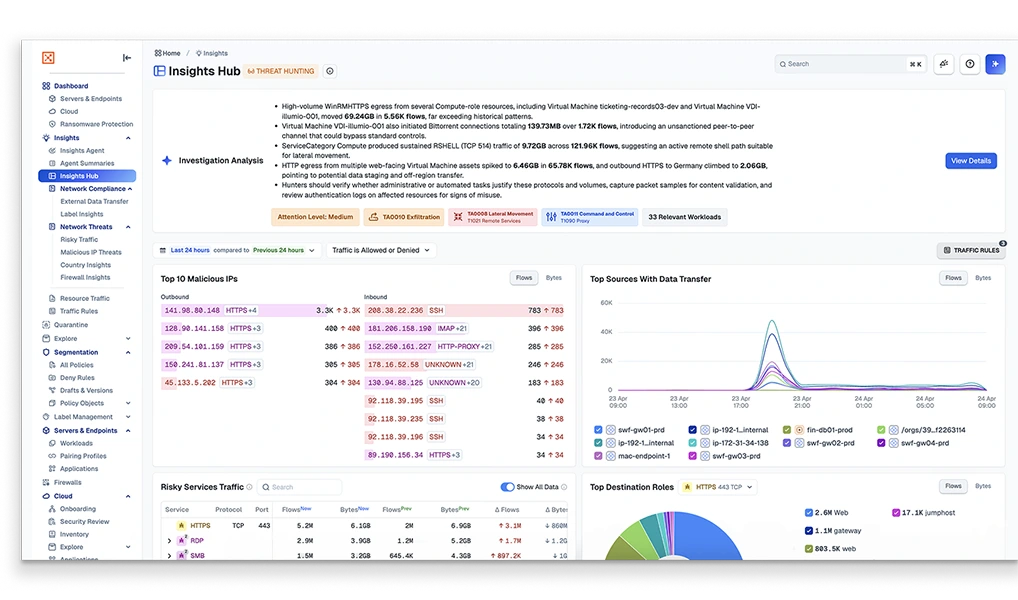
- See what’s happening across their environment in real time
- Assess risk based on actual traffic and policy alignment
- Identify unexpected lateral movement and exposed paths
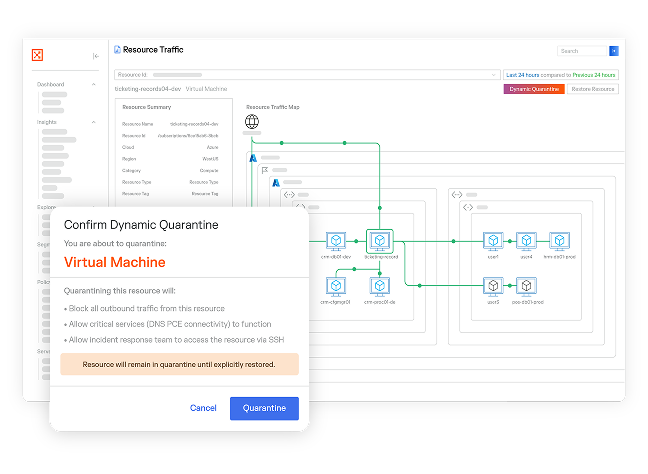
- Instantly quarantine compromised workloads — no agent required
Stop the spread — not your business.
Breaches are the new normal. Lateral movement is what turns them into disasters. Inside a flat network, every workload is reachable.
Map east-west workload communication in real time. That's the attack surface most tools aren't watching.
Microsegmentation that stops lateral movement in real time. No re-architecting. No downtime. No blinds spots.
Get demonstrable blast radius reduction and the audit trail to prove it. Compliance evidence is built in, not bolted on.
Move from prevention to resilience with your microsegmentation roadmap

The old security model — built on trust, perimeters, and stopping every breach — has run out of road. Simplifying Segmentation lays out what comes next: a practical, phased approach to microsegmentation that contains breaches, supports Zero Trust, and keeps the business running through any incident.
Try Illumio Insights at no cost
See how AI-powered breach containment helps your team do more with less.
Cathay Pacific Security Takes Flight With Illumio Microsegmentation