Move fast and don’t break things — simplified security at cloud scale
Illumio gives you real-time visibility and containment across hybrid multi-cloud environments, so innovation never comes at the cost of control.

Disruption is prevalent and costly
About 88% of organizations run production applications on public cloud infrastructure or platform services.
Of the top challenges organizations say they face or expect to face with cloud-native applications, security is the No. 1 concern.
Organizations with a mature Zero Trust strategy are 4.3 times more likely to report complete visibility into traffic across environments.
.svg)
Cloud complexity is the new attack surface
Visibility gaps, misconfigurations, and uncontrolled lateral movement leave your workloads exposed.
Modern cloud environments are dynamic — and exposed. Each new workload, container, and connection opens an entry point for attackers.

Cloud speed can hide your cybersecurity risk. Misconfigurations and unmanaged assets leave your critical systems exposed.

Securing multiple clouds is often harder than it should be. Fragmented tools and inconsistent policies can make visibility and control difficult.


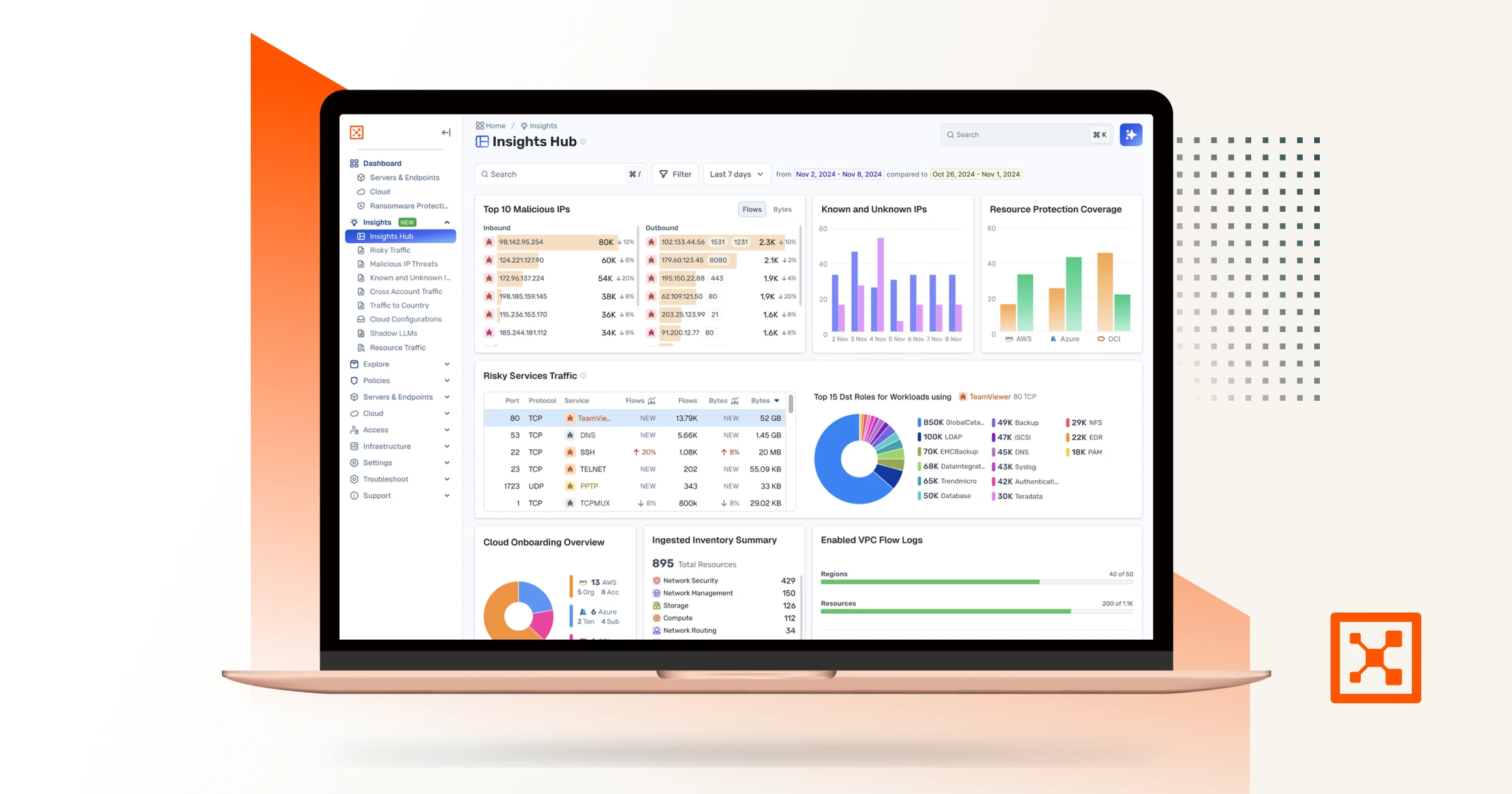
See your cloud clearly
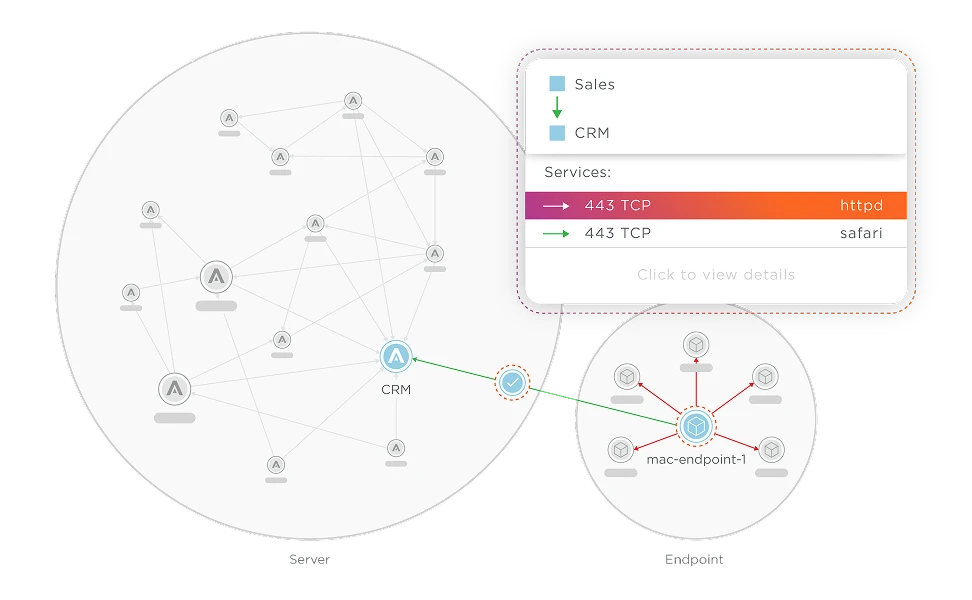
Illumio simplifies cloud sprawl, constant change, and complex interdependencies. Get a complete, real-time view of every workload, application, and dependency across hybrid and multi-cloud environments. See misconfigurations, hidden assets, and unprotected pathways — and block unwanted lateral movement.
.avif)
Contain risk, not innovation
Agility shouldn’t come at the cost of security. Illumio turns cloud complexity into control by giving you deep observability and automatically enforcing segmentation and least-privilege policies that scale. When attackers try to move, their paths are cut off instantly — without disrupting workloads or slowing down deployment.

Why organizations choose Illumio for cloud security
.svg)
Explore Illumio Insights free
See how AI-powered breach containment helps your team do more with less.

We don’t have a ‘cloud first’ policy; we have a best-of-breed policy. We build data centers and own our infrastructure – we can rack and stack – but there was no advantage to us running it internally. Illumio’s cloud solution is maintained, it’s always on the latest version, it made far more sense.
Stowe Australia