Real-time visibility and observability across the hybrid multi-cloud
Illumio turns fragmented visibility into live, actionable insight, helping you see every asset, map every flow, and spot real threats fast.


You can’t secure what you can’t see
Over half of security teams lack continuous, real-time visibility of their most critical assets.
Over a third of network traffic lacks sufficient context to support confident investigation and response.
The average financial impact of downtime from lateral movement that visibility failed to catch.
Turn blind spots into actionable insights with Illumio
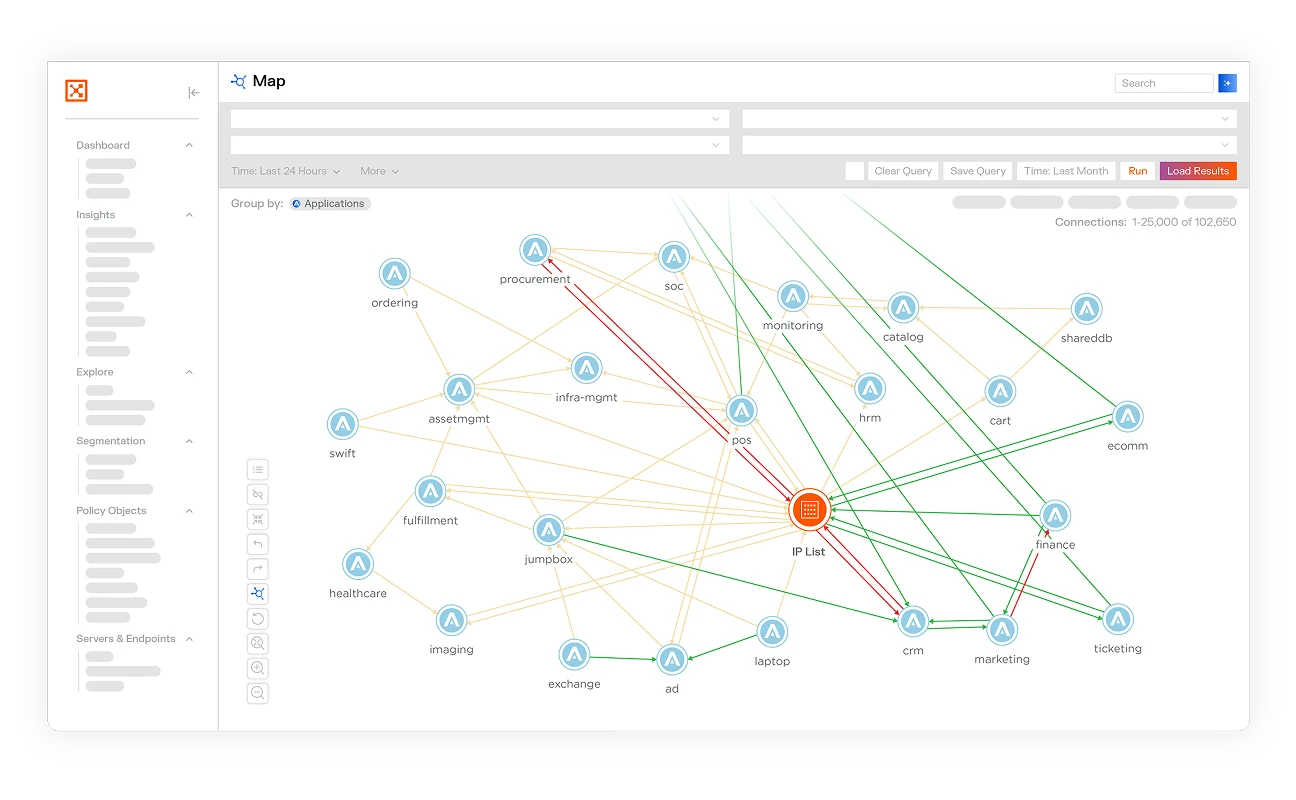
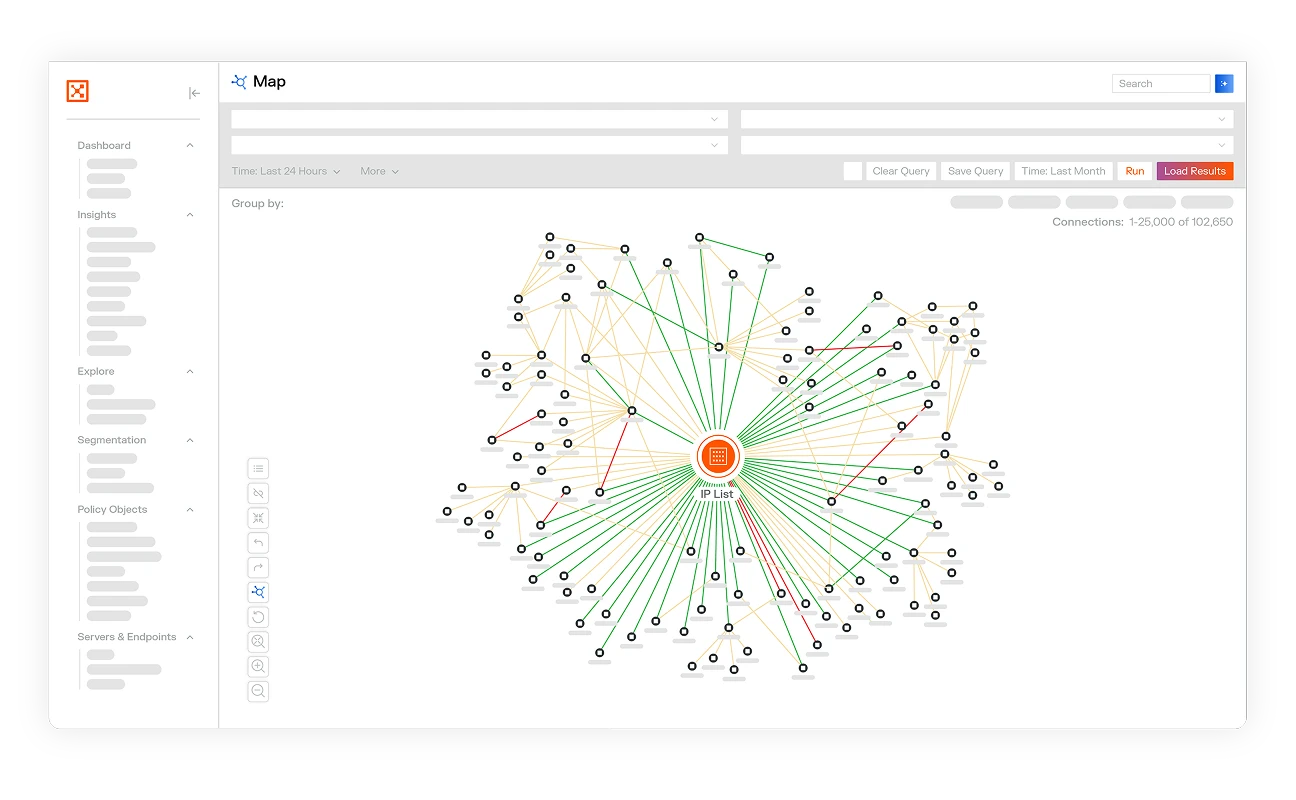
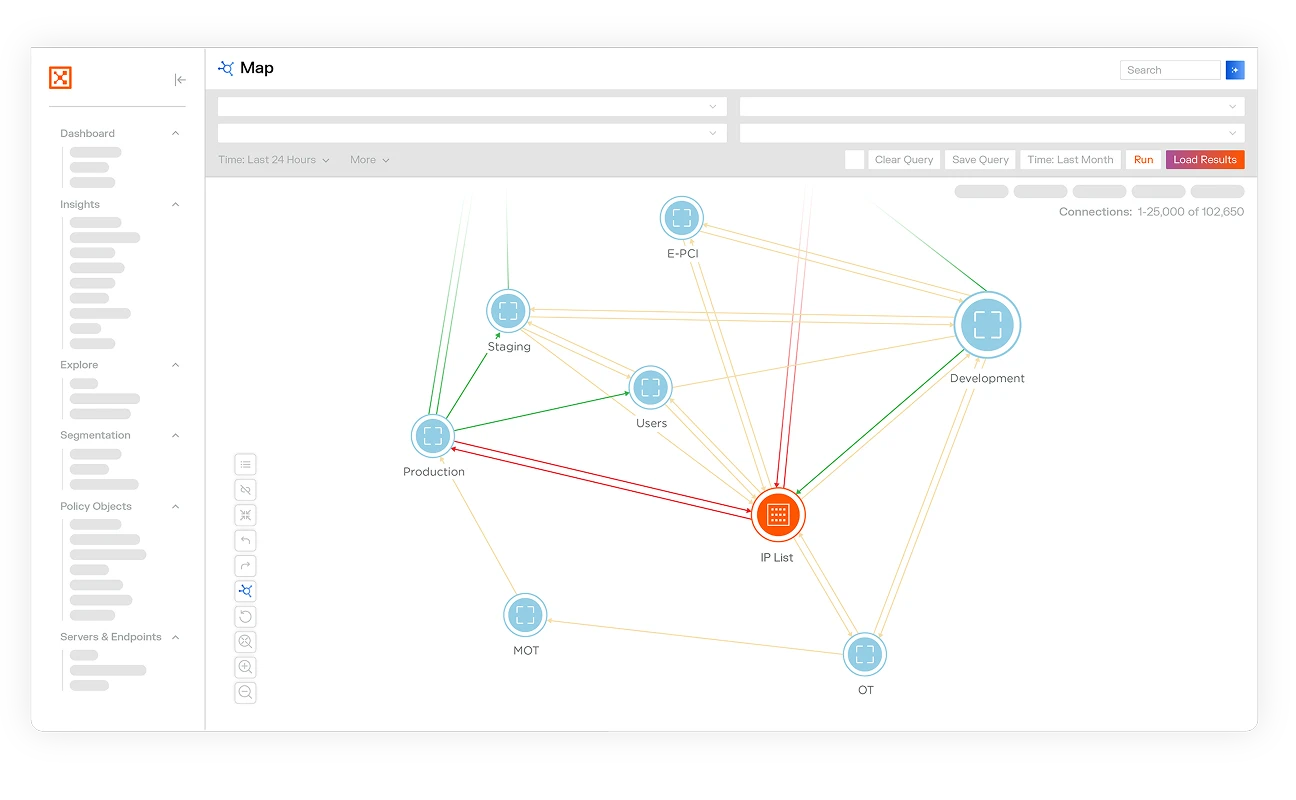
Get a live security map across your entire hybrid environment. See a dynamic view of every asset, flow, and relationship.

See what’s happening in your network and understand what’s normal, what’s high risk, and what to do about it — all visualized on your real-time map.

Map every connection across AWS, Azure, GCP, OCI, on-premises environments, firewalls, VPNs, and more.

Real-time visibility
Visibility shows you what’s happening in your environment. See what assets you have, where they live, and how they’re communicating.
With the Illumio traffic tool, get a summary of all network traffic between workloads, see a map of all traffic flows with their associated labels, and understand exactly how workloads and applications are communicating.
With the Illumio map tool, get a real-time, interactive map of all traffic flows across your hybrid infrastructure.

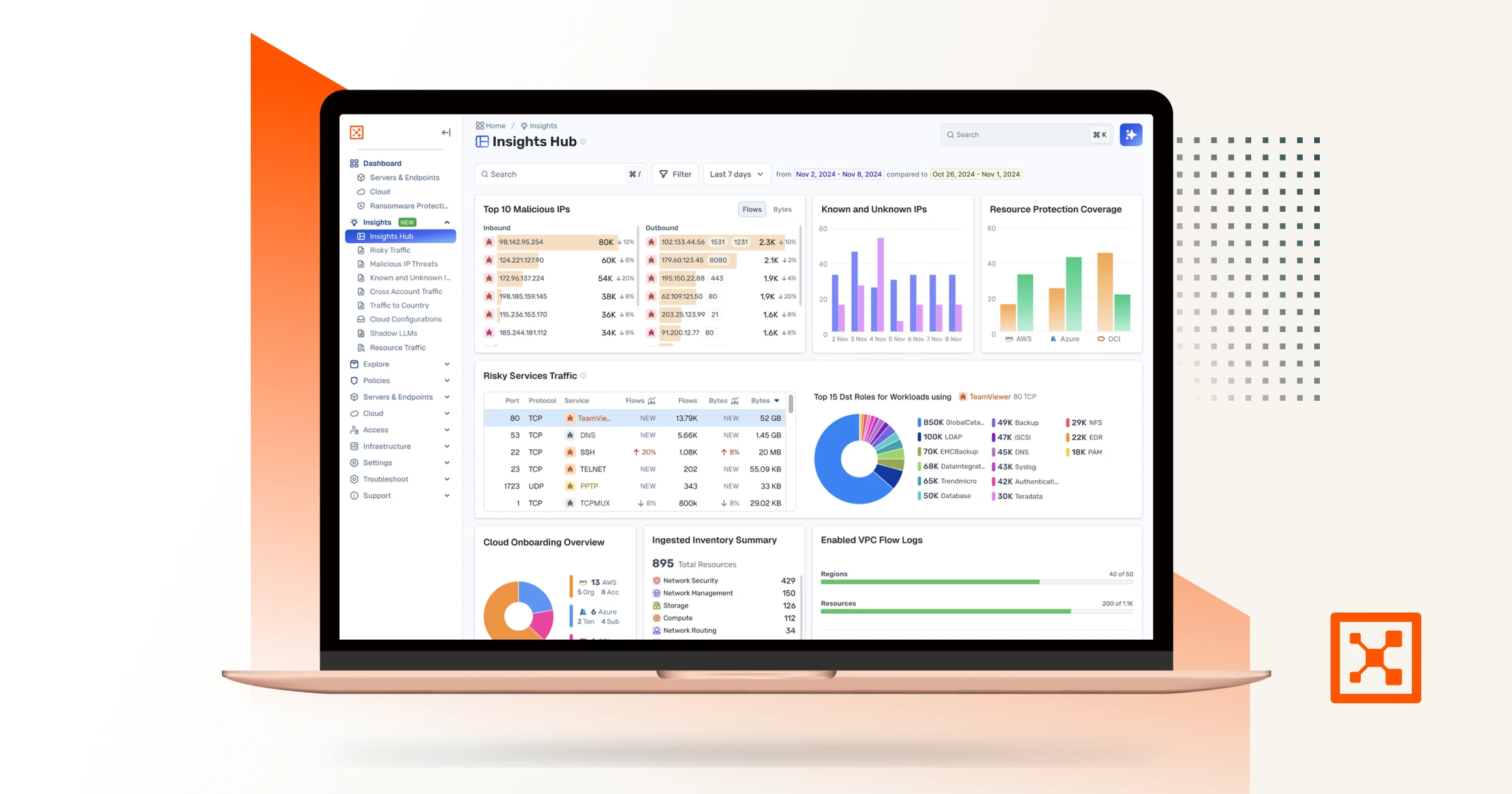
AI-powered observability
Observability takes visibility to the next level. Understand what normal looks like in your network, spot what’s high risk, and get recommendations on next steps.
Illumio Insights is built on an AI security graph to connect the dots between behaviors, vulnerabilities, and policies. Detect lateral movement, surface real threats, and contain threats fast — all in one platform.

Illumio provides unparalleled visibility in 3 hours for Mondi Group


Experience Illumio Insights today
See how AI-powered observability helps you detect, understand, and contain threats faster.