.png)

Think Like an Attacker
Why security graphs are the next frontier of threat detection and response
Cyber threats are escalating, evolving, and becoming more complex every day. Traditional security tools struggle to keep up. To defend your organization effectively, you need to adopt the mindset of an attacker. In this e-book, cybersecurity expert Dr. Chase Cunningham (Dr. Zero Trust) explains how security graphs — a revolutionary method of mapping your cyber environment — can help you uncover hidden threats, visualize risk clearly, and respond swiftly.
.webp)
You’ll learn:
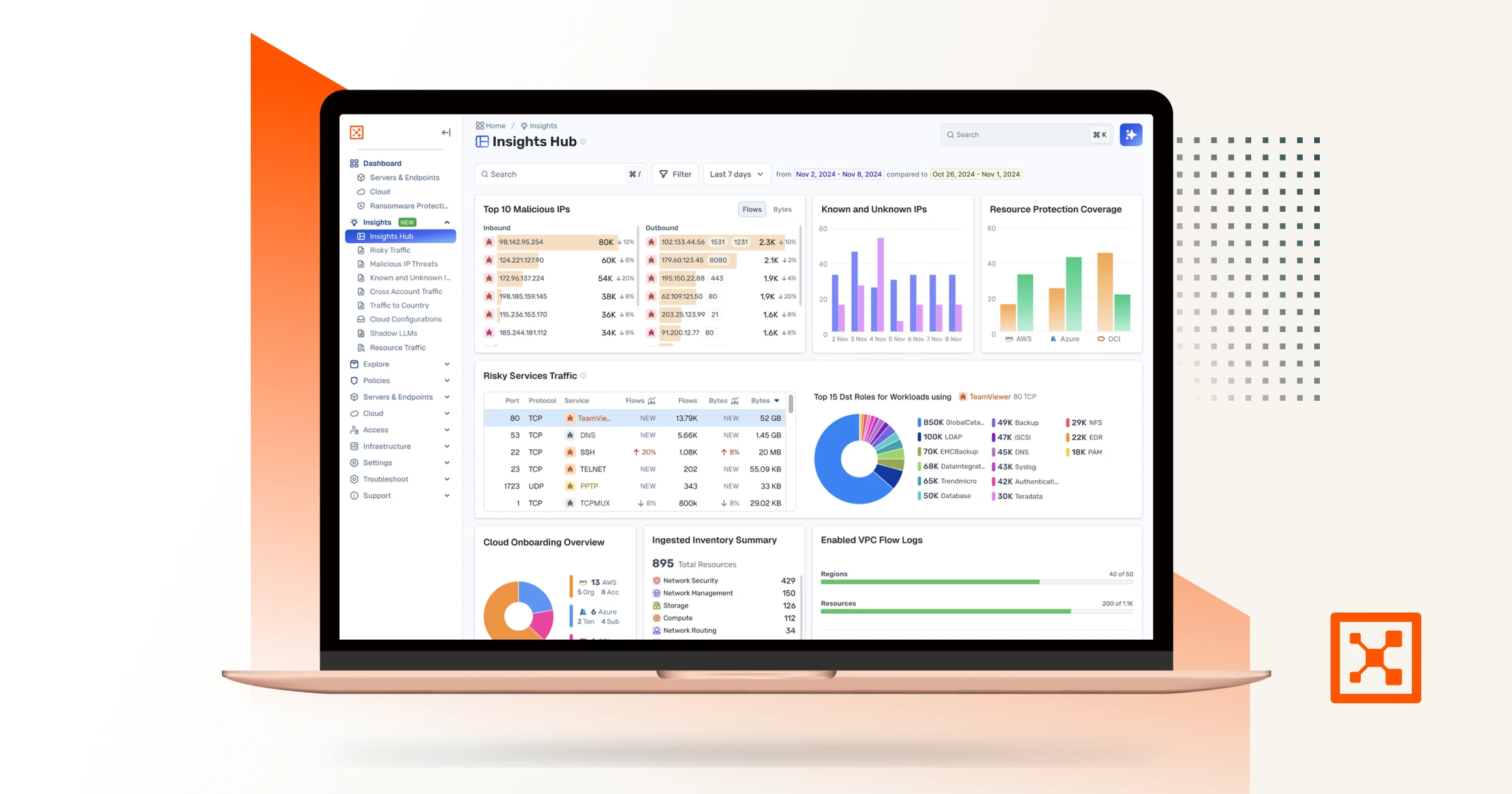
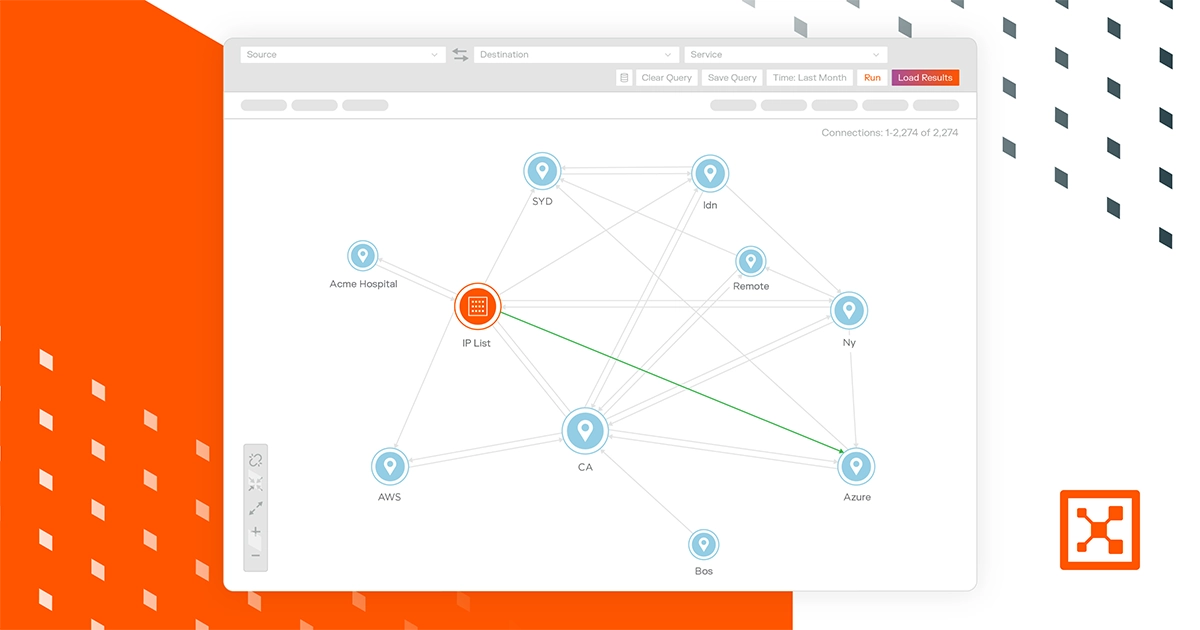
- How security graphs provide unparalleled visibility into your organization's digital landscape.
- Practical ways to detect threats earlier by visualizing hidden connections and suspicious behaviors.
- The strategic role of graph analytics in implementing a Zero Trust cybersecurity framework.
- Real-world examples illustrating how leading organizations use graph-based security to prevent breaches.
- Future trends, including how AI and machine learning will amplify the power of graph analytics in threat detection.
Get your free copy today.
Highlights
Key benefits
Asset preview
No items found.
No items found.

Gartner Hype Cycle for Cloud Security, 2021 – Representative Vendor

Forrester New Wave™ for Microsegmentation – Leader

CRN Partner Program Guide 2022 – Winner

CRN Partner Program Guide 2022 – Winner

Global InfoSec Awards - Publisher’s Choice

CRN Partner Program Guide 2022 – Winner
Assume Breach.
Minimize Impact.
Increase Resilience.
Starting with the premise that the unexpected can happen at any time drives the following behaviors