.png)

Mythos Fact Sheet
Anthropic's Claude Mythos Preview found and weaponized zero-day flaws at machine speed. Here's why breach containment is now the only viable defense.
In early 2026, Anthropic's Claude Mythos Preview AI model autonomously found thousands of critical zero-day flaws across major operating systems, browsers, and core infrastructure — and built working exploits for many of them. The time between vulnerability discovery and active exploit has collapsed to near zero.
That breaks the timing assumptions every security program is built on. Patch cycles of 30 to 90 days can't keep pace with attackers moving in seconds. Detection still runs at human speed. The old question — "Can we patch it before attackers use it?" — no longer has a useful answer. The new question is how far an attacker can move once inside.
What you'll learn:
- Why patch cycles and prevention-first models can't scale in a post-Mythos world
- How identity-driven, malware-free attacks bypass signature-based detection
- Why blast radius — not detection speed — now defines security effectiveness
- How Illumio Segmentation contains lateral movement, no matter what flaw attackers exploit
Highlights
Key benefits
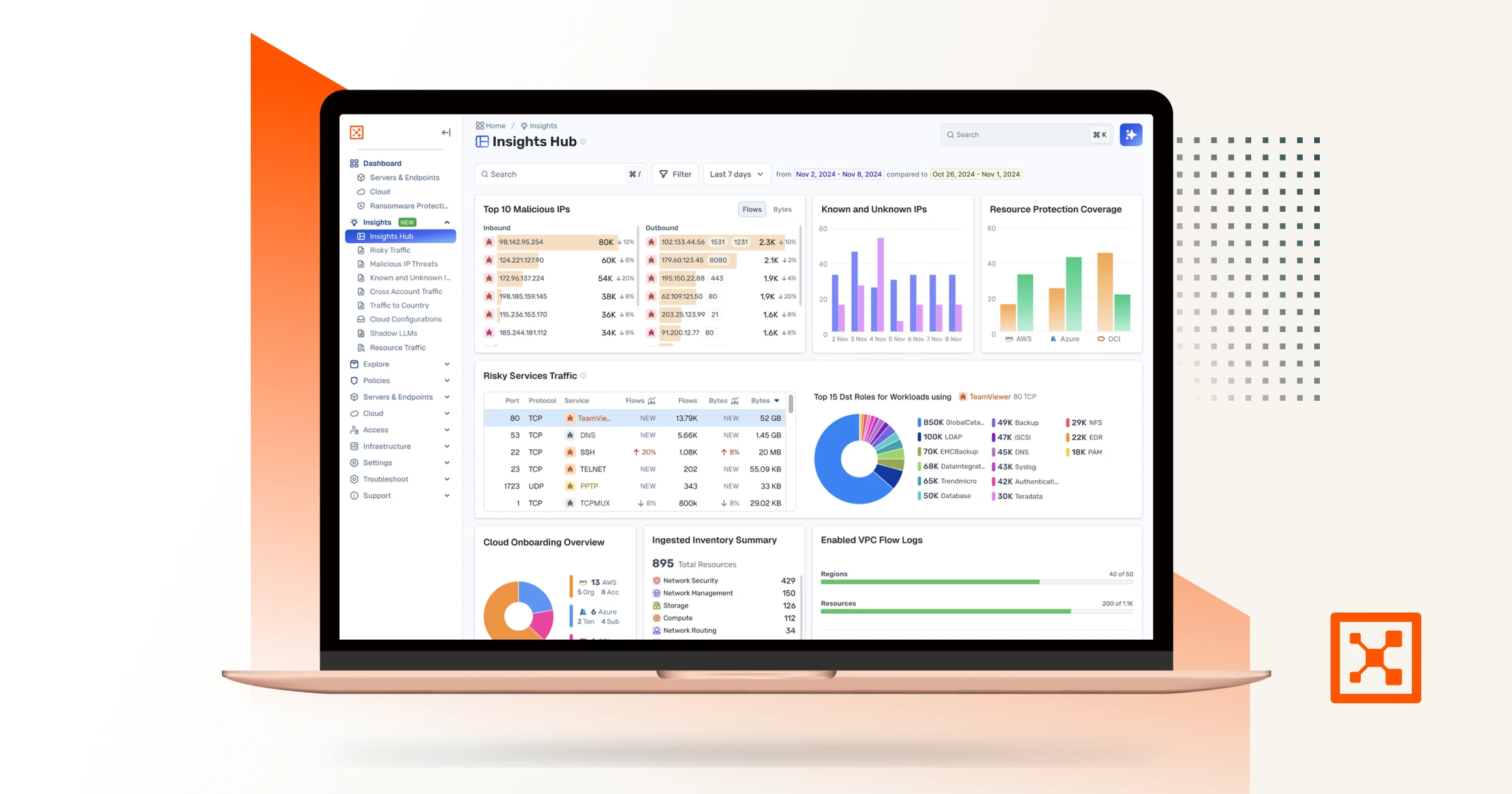
Asset preview
In early 2026, Anthropic’s Claude Mythos Preview AI model autonomously found thousands of critical zero-day vulnerabilities across major operating systems, browsers, and widely used infrastructure — and created working exploits for many of them. In Firefox alone, it turned more than 72% of the flaws it found into working exploits.
This is not a research benchmark. It ran against production code that powers the world’s servers, browsers, and firewalls. Many had been deployed for decades without anyone noticing the flaws.
Defenders working in weeks can’t keep up with attackers working in seconds.






Assume Breach.
Minimize Impact.
Increase Resilience.
Starting with the premise that the unexpected can happen at any time drives the following behaviors