.png)

The Buyer’s Guide to Detection and Response
Learn how to evaluate core detection and response technologies for today’s (and tomorrow’s) threat landscape.
Breaches are inevitable, and prevention isn’t enough anymore. You need detection and response (D&R) that gives you speed, context, and control.
But when every D&R solution makes big claims, you need to know which will truly deliver and which will just create more noise.
This free e-book breaks down today’s leading D&R tools — EDR, NDR, XDR, SIEM, and SOAR — and gives you the information you need to make the right strategy decisions for your organization.
What you'll learn:
- How to separate D&R vendor hype from real capability
- Strengths and gaps across EDR, NDR, XDR, SIEM, and SOAR
- Why traditional tools fail in hybrid and multi-cloud environments
- Why cloud detection and response (CDR) is the future of D&R
Don’t settle for incomplete protection. Download your free copy today.
Highlights
Key benefits
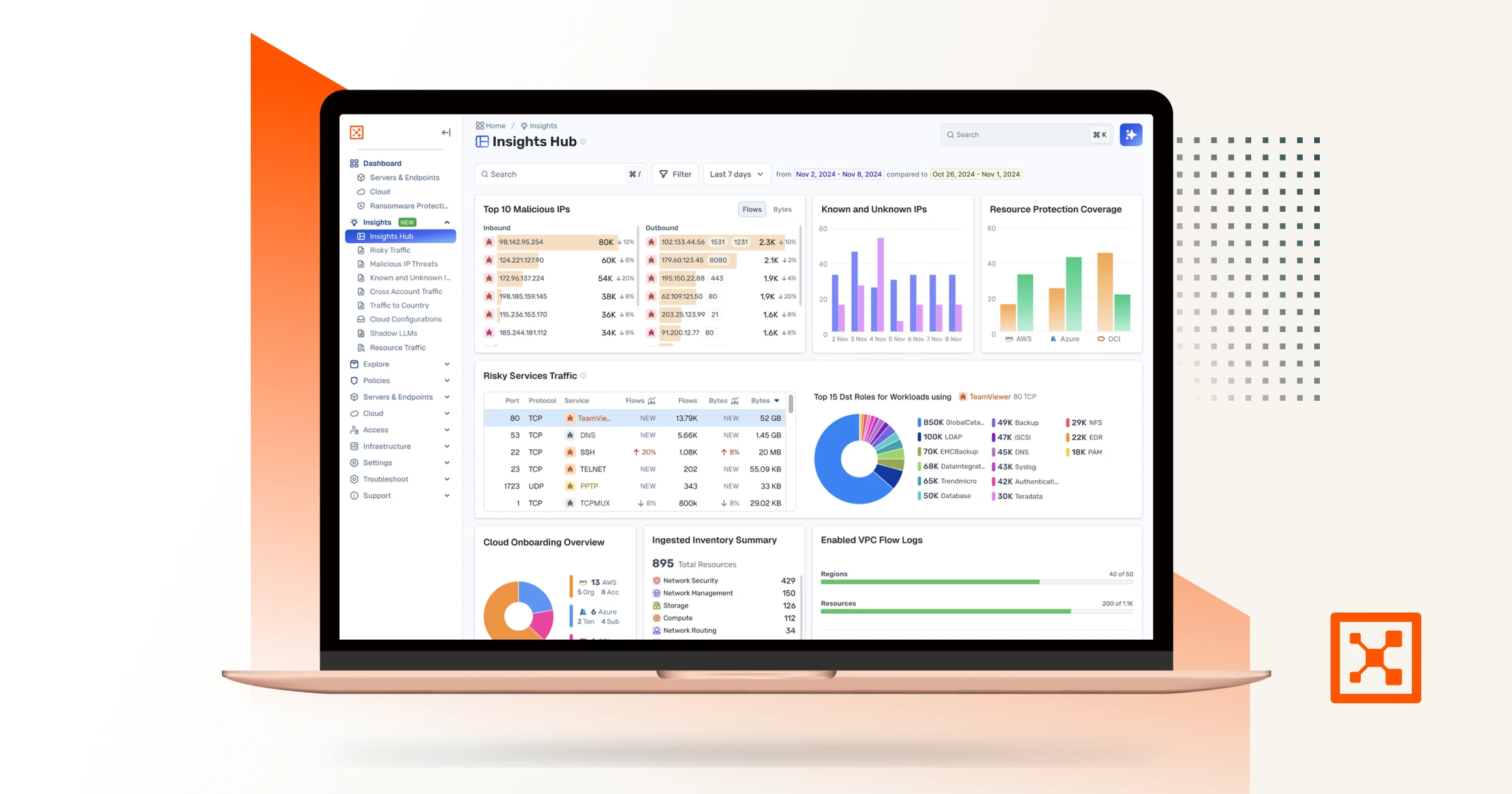
Asset preview






Assume Breach.
Minimize Impact.
Increase Resilience.
Starting with the premise that the unexpected can happen at any time drives the following behaviors