Cyber Resilience
Boost your cyber resilience with Illumio's solutions to reduce the attack surface and recover quickly from security threats.
.svg)
Related blog posts
.webp)
The Modern SOC Is Built on a Broken Foundation. Zero Trust Can Fix It.
Discover why SOC outcomes haven’t improved in 20 years, and how Zero Trust fixes the architectural problems no detection tool can solve.
.webp)
Top Cybersecurity News Stories From May 2026
Track May 2026’s top cybersecurity stories, from AI-powered cyber threats to ransomware resilience and new federal oversight strategies.
%20(1).webp)
Agentic AI Security: How Illumio and Netskope Help You Adopt It Safely Without Trusting It Blindly
Discover how Illumio and Netskope work together to help organizations adopt agentic AI safely with segmentation and AI agent governance.
.webp)
More Spend, More Breaches: The Uncomfortable Truth About Cybersecurity ROI
Understand why the cybersecurity ROI model is failing and how CISOs can reframe the board conversation around resilience, not prevention.
.webp)
The Mythos Readiness Checklist: Steps to Protect Your Network from AI-Driven Threats
Prepare your network for AI-driven cyberattacks with the Mythos readiness checklist, covering visibility, microsegmentation, and breach containment.
.webp)
Words That Work: Virgin Money CISO Neil Robinson on Speaking Security to Power
Learn how Virgin Money CISO Neil Robinson translates complex cyber risk into plain language that drives board-level action and keeps security programs funded.

What Project Glasswing Means for the People Running Cybersecurity
Understand how Project Glasswing and AI-driven vulnerability discovery powered by Mythos are reshaping cybersecurity and why breach containment with segmentation is now critical.
Mythos: Time to Rewrite the Entire Cybersecurity Model
Rethink cybersecurity for the AI era as machine-speed attacks outpace human defenses, making resilience and breach containment essential for survival.
.webp)
The Future of Cybersecurity Is Anti-Fragile, Not Just Resilient
Learn why anti-fragile cybersecurity goes beyond resilience and how Zero Trust helps systems adapt, reduce risk, and improve after every attack.
.webp)
Japan’s Cloud Security Reality: Efficient on the Surface, Exposed Where It Matters Most
Discover how Japan’s efficient cloud security environments can hide lateral movement risks when visibility gaps leave east-west traffic and hybrid activity exposed.
.webp)
A Former White House CIO on Why Zero Trust Must Be Designed for How People Actually Work
Improve your Zero Trust strategy by focusing on user behavior to reduce cyber risk and deliver better security outcomes.
.webp)
Cybersecurity Is Broken: Why Outcomes Aren't Improving and What Needs to Change
Rethink modern cybersecurity and prioritize breach containment to stop lateral movement, limit blast radius, and protect critical assets from modern attacks.
Related resources








The Big Book of Breaches
The year’s most devastating attacks, how they happened, and what you can do about them







Mythos Fact Sheet
Anthropic's Claude Mythos Preview found and weaponized zero-day flaws at machine speed. Here's why breach containment is now the only viable defense.







The Containment Gap: Exploring the Distance Between Detection and Resilience
Uncover the containment gap between detecting threats and stopping breaches, and learn why fast isolation defines modern cyber resilience today worldwide.
.webp)







The Illumio Breach Containment Platform
Detect, assess, and stop lateral movement across your hybrid environment with a single platform.
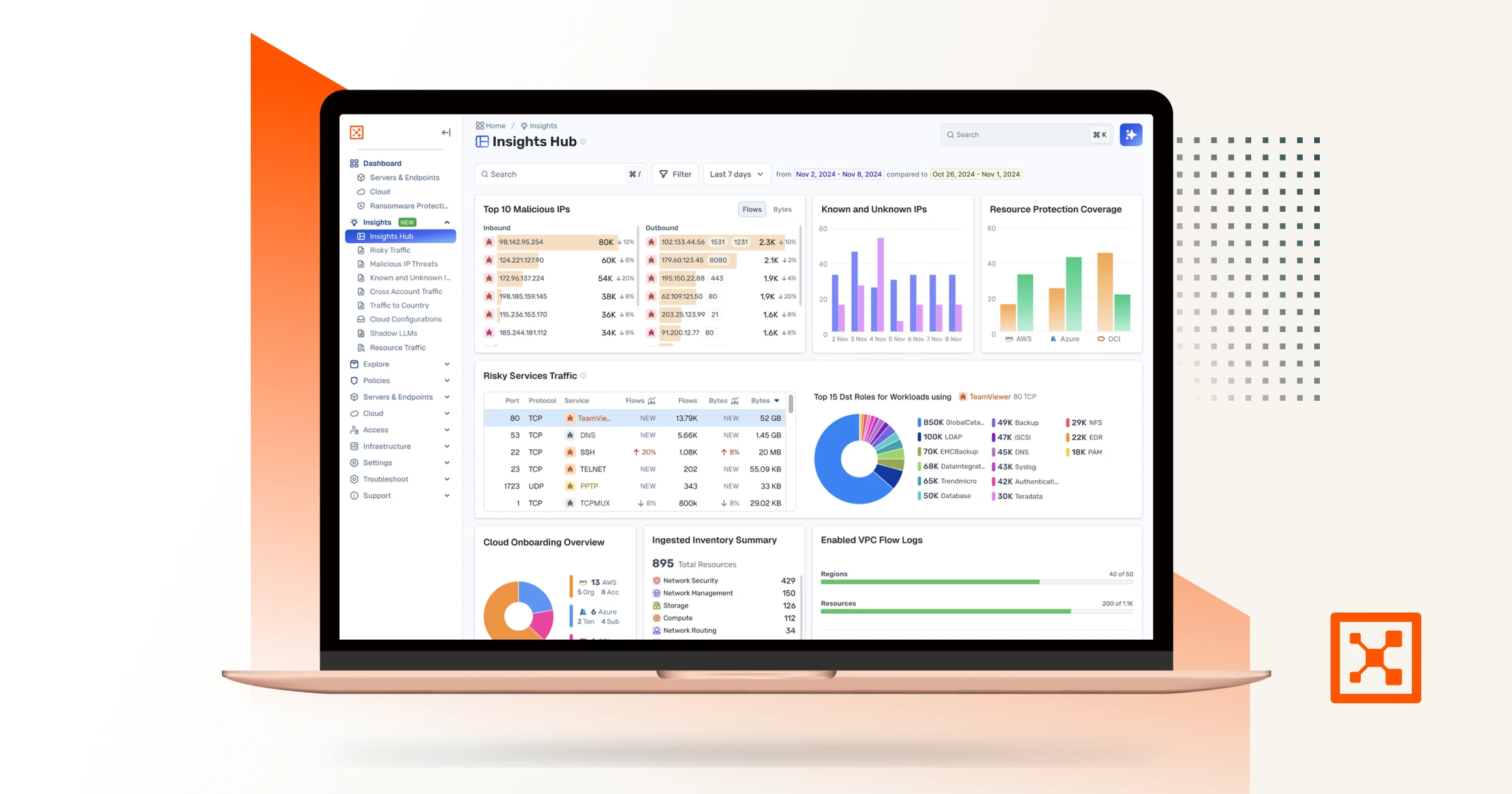







Illumio Insights
Learn about hybrid multi-cloud detection and responsesolution built on an AI-powered security graph







Getting Started with Security Graphs: A Roadmap to Resilience
How security graphs can help you detect threats faster, strengthen Zero Trust, and make better risk decisions








Illumio Insights Explainer Video
DiscoverAI-powered hybrid cloud detection and response (CDR) that identifies lateral movementrisks, detects attacks, and contains instantly across your hybrid multi-cloud –with Discover how Insights identifies lateral
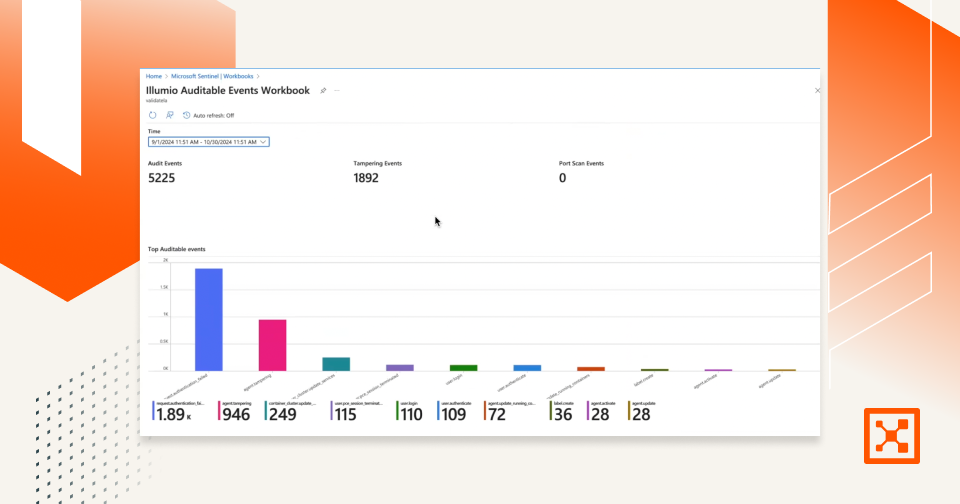







Illumio Sentinel Integration Demo
Watch how Illumio's integration with Microsoft Sentinel streamlines SecOps, strengthens compliance, and accelerates cyber incident response.








The Cloud Resilience Playbook
Learn how to combat, contain, and conquer breaches in the cloud with microsegmentation.
Assume Breach.
Minimize Impact.
Increase Resilience.
Ready to learn more about Zero Trust Segmentation?