NDR vs. Illumio Insights: Detecting and Containing Lateral Movement in the Hybrid Cloud
For years, network detection and response (NDR) platforms have served as the security team’s microscope.
They inspect network traffic at the packet level, analyze behavior across infrastructure, and surface suspicious activity hidden inside complex environments. When something goes wrong, NDR tools help investigators reconstruct what happened.
That capability made sense when most applications lived inside data centers and traffic flowed through predictable network paths.
Modern infrastructure no longer works that way.
Applications now run across hybrid environments that span on-premises systems, multiple clouds, containers, APIs, and short-lived workloads. And attackers have adapted to this complexity.
Instead of attacking the perimeter, they slip inside through stolen credentials, exposed services, or misconfigurations. Once they gain a foothold, the real attack begins as they move laterally across the environment.
In that moment, understanding what happened yesterday isn’t enough. Security teams need to see risky communication patterns in real time and stop attackers before they expand their access.
That shift exposes the limits of traditional NDR. Today’s modern environments require a new approach to detection and breach containment.
That’s where Illumio Insights enters the picture.
Illumio Insights: detection built for breach containment
Illumio Insights takes a different approach to threat detection and response.
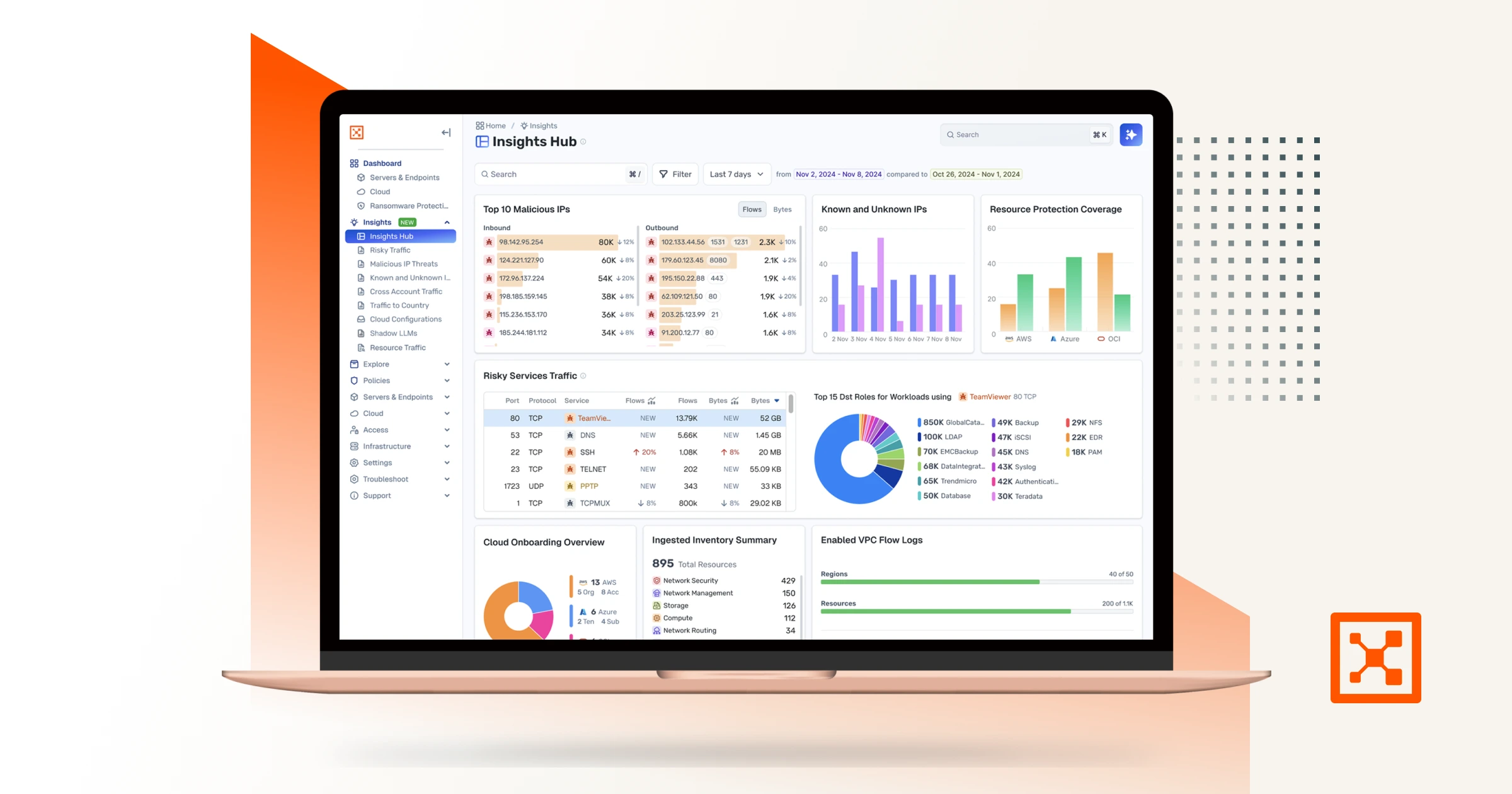
Instead of relying on packet capture and reconstructing traffic after an incident, Insights analyzes live communication patterns across the environment. It ingests flow data from cloud platforms, on-premises systems, and hybrid infrastructure to build a real-time map of how workloads interact.
At the center of this capability is the Illumio AI security graph.
The graph models relationships between systems and continuously evaluates them for risky communication patterns, suspicious connections, and signs of lateral movement.
This allows Insights to surface and prioritize risk before attackers can exploit it. Security teams can see suspicious activity as it happens instead of reconstructing events later.
Insights also simplifies investigation.
Traditional detection platforms generate large volumes of alerts that require manual analysis. Within Illumio Insights, the Insights Agent acts as an AI assistant that helps analysts focus on what matters. It analyzes detections, prioritizes risk, maps findings to MITRE ATT&CK techniques, and recommends actions to address the threat.
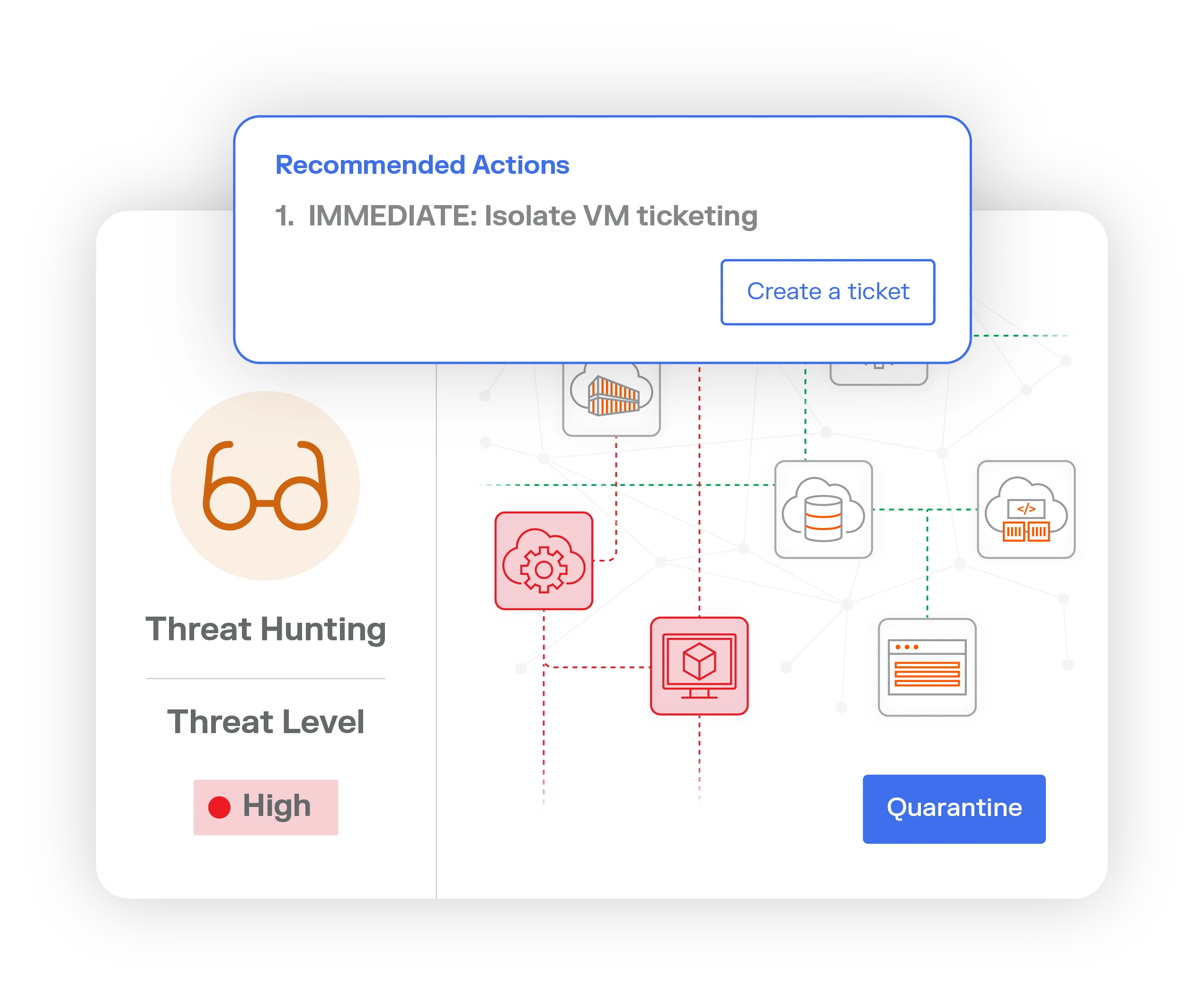
But the biggest difference appears after detection. Most NDR tools stop at identifying threats, while Illumio focuses on containing them.
Insights integrates directly with Illumio Segmentation to enforce network-level controls that stop attackers from moving laterally across the environment. Security teams can isolate compromised workloads, block risky communication paths, and prevent attackers from expanding access.
Detection reveals the threat, but containment stops the breach.
What NDR platforms were designed to do
At the heart of every NDR platform is deep packet inspection (DPI).
These solutions rely on network sensors that analyze traffic flowing across a network in real time. Some sensors are virtual, while others are physical devices plugged directly into data center infrastructure.
As packets move across the network, NDR solutions capture and analyze them at extremely high speeds. They can decrypt traffic, inspect payloads, and examine every detail of the communication stream.
But storing every packet would require enormous storage capacity. This requires NDR platforms to take a different approach.
Instead of storing raw traffic, they extract key details about what occurred and save those details as metadata. That metadata becomes a searchable historical record of network activity.
If something suspicious happens, security teams can go back and reconstruct what happened — which systems communicated, what data moved, and how the event unfolded.
This forensic capability is incredibly powerful. In fact, for some industries that rely on on-premises data center networks, such as banking and some federal agencies, it’s mandated by compliance regulations. These organizations must maintain detailed network records for investigation and compliance purposes.
In those environments, NDR solutions provide exactly what teams need: a detailed historical view of network activity.
Where NDR begins to struggle
The architecture that makes NDR solutions powerful also reveals its limitations.
Most NDR platforms were built specifically for on-premises data center networks. Their sensors sit inside the network and analyze traffic flowing through physical infrastructure.
That design works extremely well in traditional environments. But modern infrastructure looks very different.
Organizations now run applications across hybrid environments that combine on-premises systems, multiple clouds, and container platforms.
And while NDR vendors have added cloud support over the years, those capabilities are often bolt-on additions rather than core design features. As a result, their strongest capabilities remain inside the data center.
That creates several challenges.
Detecting threats in the cloud is weaker
In cloud environments, NDR platforms typically rely on cloud flow logs rather than deep packet inspection.
Flow logs provide visibility into network communication. But they lack the packet-level detail that NDR platforms depend on for detection.
This means the threat detection capabilities that work well on-premises often don’t translate cleanly into cloud environments.
For organizations running hybrid infrastructure, this creates blind spots.
Detection is still investigation-heavy
Many NDR vendors have added machine learning and AI capabilities to help identify anomalies. They baseline network behavior and look for unusual spikes or deviations from normal traffic patterns.
If something unusual happens, the system generates an alert. Once that alert appears, though, the burden shifts back to human analysts.
Security teams must investigate the event, determine whether it represents malicious activity, and decide how to respond.
The tool surfaces the signal, while humans still do the heavy lifting.
The focus is still historical analysis
NDR platforms excel at helping teams investigate what happened in the past.
That capability is valuable for forensic analysis, regulatory reporting, and post-incident investigation.
But modern attacks move quickly. By the time teams reconstruct events, the attacker may have already expanded access across the environment.
Why many organizations use NDR anyway
Despite these limitations, NDR tools remain widely deployed.
In some environments, they’re required. Certain government agencies and highly regulated industries such as banking must use deep packet inspection to meet compliance requirements. For those organizations, NDR is non-negotiable.
For other organizations, NDR is simply the closest available tool for network threat detection. They may not need full packet-level inspection or long-term forensic records.
What they really need is the ability to detect suspicious activity across their network. In those environments, deep packet inspection can be overkill. It collects enormous amounts of information and requires significant infrastructure to operate.
Yet many organizations deploy it anyway because there hasn’t been a better option.
That’s where Illumio Insights enters the picture.
Rethinking network detection for hybrid environments
NDR remains a powerful tool for organizations that require deep packet inspection and historical forensic visibility. But many organizations today operate in environments NDR was never designed to protect.
Hybrid infrastructure, ephemeral workloads, and cloud-native architectures demand a different approach.
Security teams need to detect risky communication patterns across the entire environment and respond before attackers can spread.
Illumio Insights provides that capability.
By combining real-time detection, AI-driven analysis, and built-in segmentation, it helps organizations move beyond investigation and toward true breach containment.
Try Illumio Insights free to see risky communication across your environment and stop attackers from moving laterally.