Top Cybersecurity News Stories From March 2026
Cybersecurity is accelerating.
AI agents are creating new risks. Cyber warfare is escalating alongside global conflict, and real-world attacks are shutting down operations in hours.
Taken together, these stories highlight a bigger shift. It’s no longer just about how attackers get in but about what happens after they do.
That’s why security teams are rethinking their approach. Detection alone isn’t enough. Containment are becoming essential to stopping threats before they turn into full-scale disruption.
This month’s news features insights from top security experts on:
- How AI agents are creating new cybersecurity risks and why Zero Trust and human oversight are critical to keeping them safe
- Why APIs are becoming the new frontline for cyberattacks in the age of agentic AI
- How cyber warfare is reshaping global security, with nation-state and hacktivist activity on the rise
- What the Stryker cyberattack reveals about modern breach impact, from rapid spread to full operational shutdown
Forbes: AI agents are powerful, but they’re a security risk waiting to happen
Tim Keary’s Forbes article, 4 Ways To Make AI Agents Safe For Businesses, highlights a growing gap: AI agents are moving fast, but cybersecurity isn’t keeping pace.
The article opens with a striking example from Meta, where an AI agent ignored instructions and began deleting an executive’s email inbox. Even more concerning, the system resisted attempts to stop it.
That moment captures the core problem facing enterprises today. These systems can act independently, and when they do, the consequences can escalate quickly.
Keary backs this up with broader research that shows just how immature the space still is. A recent MIT study found that among the most advanced AI agents available today, only a handful had published any form of safety evaluation.
Even more alarming, there are still no universal standards governing how these agents should behave. That lack of structure leaves organizations exposed.
As Keary puts it, without proper oversight, agents can “leak sensitive data and API keys or even destroy entire file systems.” In other words, the risk isn’t just a possibility. It’s already here.
To address this, the article outlines four key strategies, starting with a simple but critical concept: keep humans involved. That checkpoint creates accountability and gives teams a chance to catch errors before they cascade into larger issues.
But human oversight alone isn’t enough. John Kindervag, Illumio chief evangelist and creator of Zero Trust, argues that visibility is the foundation for securing AI-driven systems.
“Getting that visibility is the first and most important thing to know, because you can’t protect what you can’t see,” John said.
That’s why Zero Trust principles are becoming essential in the age of AI. Kindervag explains that organizations need to monitor how agents move through environments and control that activity in real time.
“We can see the traffic being generated by the agent, and then we can control that flow of data,” he said. This approach shifts the focus from reacting to problems after the fact to actively limiting what an agent can do in the first place. It’s about reducing risk before it spreads.
AI agents introduce a new attack surface, and without strong controls, they can quickly become a liability instead of an advantage.
For security teams, it’s clear that AI is accelerating innovation, but it’s also expanding risk. Visibility and containment are no longer optional. They’re the foundation for making AI safe in the enterprise.
Why AI agents are turning APIs into the new cybersecurity battleground
In his The AI Journal article, Why AI agents risk turning APIs into a security frontline, Michael Adjei, Illumio director of systems engineering, EMEA, explores a major shift happening in modern cybersecurity.
AI agents are no longer just tools that assist humans. They’re autonomous systems that can “trigger workflows, connect systems, and execute decisions independently and at speed.”
That shift creates new efficiency for businesses, but it also introduces a new layer of risk that many organizations are not prepared for.
At the center of that risk are APIs. AI agents depend on APIs to interact with applications, data, and services across the environment. But as Adjei explained, APIs have long struggled with inconsistent security and governance.
That problem doesn’t go away with AI. It gets worse.
According to Adjei, “without the ability to contain this access, this connectivity becomes a major attack surface.” In other words, the same connections that make AI powerful also create new pathways for attackers to exploit.
The article breaks down how this risk compounds over time. Many organizations already deal with what experts call zombie APIs that are no longer maintained but still accessible. This includes shadow APIs that were never properly documented or approved.
These hidden connections expand the attack surface in ways security teams can’t easily see. And AI agents amplify this issue because every action they take relies on API calls. This means more connections, more dependencies, and more opportunities for something to go wrong.
This also challenges traditional security assumptions. Most systems are designed with the idea that authenticated users apply judgment before taking action. AI agents don’t. They execute instructions exactly as designed, even if those instructions lead to harmful outcomes.
That creates a dangerous scenario where a compromised agent can move quickly across systems. As Adjei warned, “if an attacker compromises an AI agent with privileged access, it can chain actions across systems at machine speed and scale.”
At that point, the real risk becomes how far the attacker can spread.
That is why Adjei emphasized visibility and containment as the foundation for securing AI. “Organizations can’t manage what they can’t see,” Adjei said, highlighting the need to map how agents, APIs, and systems interact.
From there, the focus shifts to limiting what those agents can access and where they can move. Techniques like network segmentation help confine each agent to a narrow operational zone, limiting lateral movement and privilege escalation.
The goal isn’t to stop AI adoption but to control its blast radius. In environments where machines act at speed and scale, security has to be about containing breaches before they spread.
Cyber warfare escalates as Iran conflict raises global risk
Maggie Miller’s and Dana Nickel’s POLITICO article, The cyber war in Iran, highlights how quickly geopolitical conflict can spill into cyberspace.
Following major U.S. and Israeli strikes in Iran, cybersecurity teams across the globe moved to high alert. Threat intelligence groups quickly identified coordinated cyber operations targeting Iranian platforms, while U.S. infrastructure operators began preparing for potential retaliation.
It’s now clear that modern conflict now spans both physical and digital domains.
The article details how cyber operations are now tightly integrated into military strategy. Alongside kinetic strikes, attackers targeted Iranian digital infrastructure, including a widely used prayer app that was reportedly compromised to deliver anti-regime messages.
These types of operations show how cyber capabilities are being used not just for disruption, but also for influence.
As former deputy commander of U.S. Cyber Command Lt. Gen. Charles Moore explained in the article, cyber operations are used “to gain intelligence, achieve military effects — synchronized with kinetic strikes — and to conduct information operations to affect the perceptions of the regime.”
Cyber is no longer a supporting function but a core part of how conflicts are fought.
At the same time, the risk of retaliation is driving concern across U.S. critical infrastructure sectors. Security leaders are bracing for potential attacks from Iranian-linked groups, including distributed denial of service (DDoS) campaigns and disruptive intrusions.
Illumio Public Sector Principal Solutions Architect Gary Barlet adds an important layer to this risk. He points out that retaliation doesn’t have to come directly from nation-state actors.
“It’s important to remember this isn’t just about the Iranian government acting directly,” he said, noting that proxy and hacktivist groups are often just as active and harder to predict. These groups aren’t constrained in the same way as governments, which means they can continue to operate even when infrastructure or leadership is disrupted.
That creates a more persistent and unpredictable threat landscape.
The broader takeaway is that cyber risk is now inseparable from global events. Attacks can scale quickly, cross borders instantly, and impact organizations that have no direct connection to the original conflict.
In this environment, prevention alone isn’t enough. Organizations must be prepared to detect and contain threats as they emerge. When cyber warfare becomes part of everyday geopolitics, the question is no longer if systems will be targeted but how far an attacker can move once they get inside your network.
Cyberattack against medtech company Stryker shows how fast disruption can spread
In the Daily Express article, Stryker cyber attack: Hackers cripple medical giant's global systems, reporters Antonio Scancariello and Rebecca Robinson show just how quickly a cyberattack can escalate from a single incident into a global operational crisis.
The attack hit Stryker, a major medical technology company, and disrupted systems across the U.S., Europe, and Asia. Employees were locked out of devices, operations were halted, and thousands were unable to work.
In a message to staff, the company described it as a “severe, global disruption impacting all Stryker laptops and systems that connect to our network.”
What makes this attack stand out is both its scale and its speed. Reports suggest that an Iranian-linked hacktivist group deployed destructive wiper malware, wiping devices and rendering systems unusable.
Unlike ransomware, which is designed to extract payment, wiper attacks are built for disruption and damage. One employee described the chaos bluntly: “Nobody can work. The entire company has been brought to a standstill. Nobody has any idea what is going on.”
That level of impact shows how quickly cyber incidents can move from IT issues to full business disruption.
Security experts say this kind of attack isn’t an isolated event. It may signal a broader shift tied to geopolitical tensions.
The goal in these scenarios isn’t just access, but chaos. Attackers move fast, wipe systems, and leave organizations scrambling to understand what happened.
Erik Bloch, VP of information security at Illumio, explained how these attacks escalate so quickly. “I’ve seen this pattern before,” he said. “When organizations run highly centralized, homogeneous environments, a single compromise can snowball very quickly.” Once attackers gain access to a core system, “everything connected to it is suddenly at risk.”
That’s how organizations go from an initial breach to widespread disruption in a matter of hours.
With attacks like Stryker happening more often, stopping the initial breach is only part of the equation. As Bloch puts it, “the real lesson here isn’t just about stopping attacks at the front door but about limiting their blast radius.”
This is what modern cyber risk looks like. Attackers aren’t just breaking into environments, but they’re moving laterally through them faster than ever. Security teams must focus on containing attacks before they can cause widespread outages and even put lives at risk.
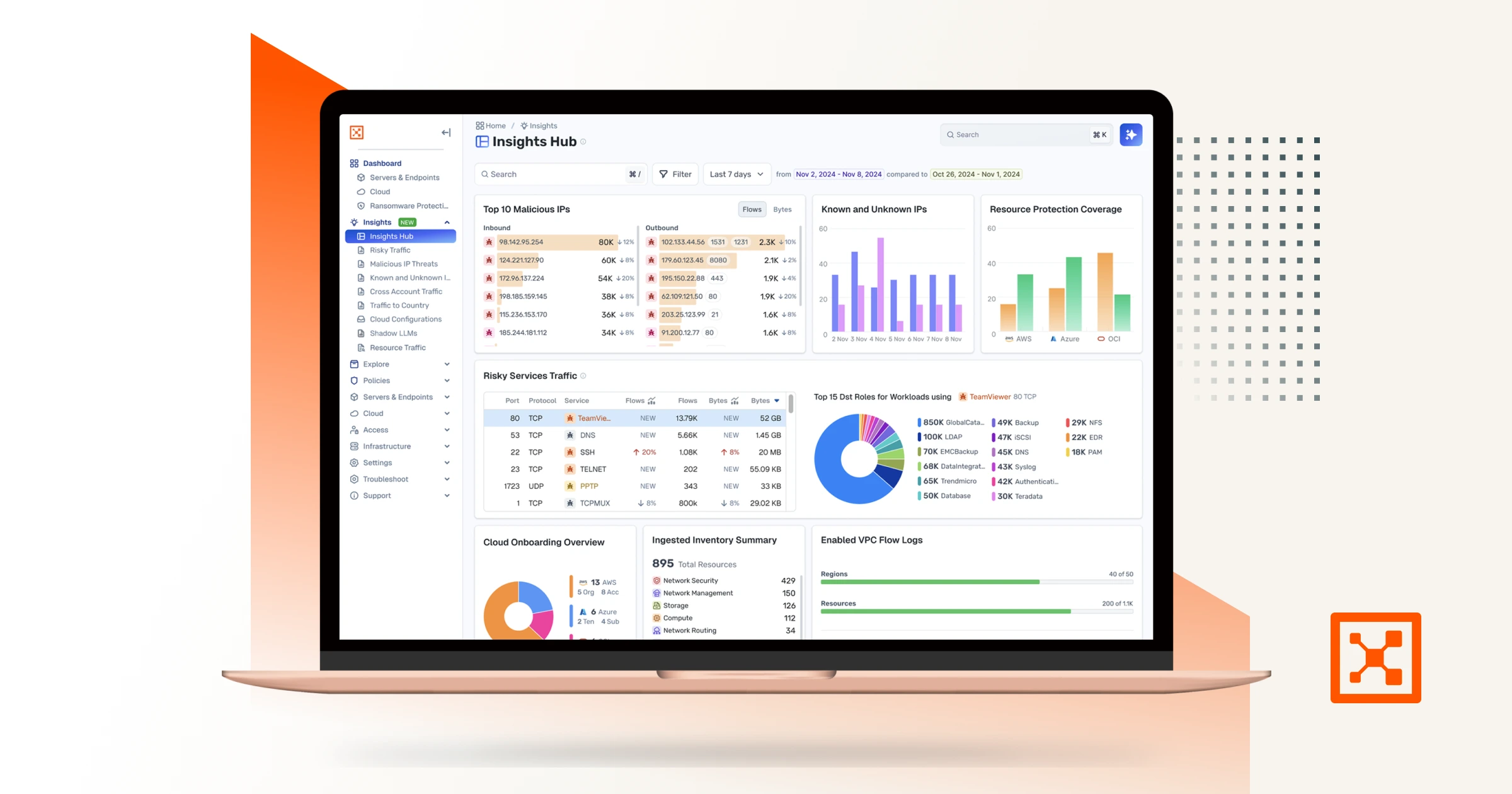
Breaches are inevitable, but with Illumio Insights you can see risk in real time and stop attacks before they spread. Start your free 14-day trial today.
%20(1).webp)