The Ultimate Guide to Zero Trust
Let’s dive into one of the biggest changes in security today: Zero Trust. It’s not just a trendy term—it’s a whole new way of thinking about keeping data safe and building trust in the digital world. Whether you’re new to Zero Trust or an IT expert looking to learn more, this guide has you covered.
What is Zero Trust?
Zero Trust is a cybersecurity approach built on one main idea: never trust, always verify. Unlike older methods that focus on protecting the network’s perimeter, Zero Trust assumes threats can come from anywhere — inside or outside the network.
Put simply, Zero Trust means you don’t assume anything is trustworthy. It’s not about being paranoid — it’s about being ready.
Zero Trust principles:
Zero Trust is built on a few key ideas:
- Assume breach: No part of the network is trusted. It’s impossible to prevent every breach — breaches are inevitable. Organizations must prepare for the next inevitable breach.
- No implicit trust: Every user, device, and app must prove they are who they say they are. This makes sure only approved and verified people or systems can access your network. It removes the outdated idea that everything inside the network is safe. By checking identities regularly, it helps protect against insider threats and stolen login information.
- Least-privilege access: Everything in the network — devices, users, flows, data — should only get access to what they need to do their job. This lowers the chances of them accidentally or intentionally accessing critical resources. By keeping access limited, organizations can make it harder for attackers to spread through the network which reduces the impact of a breach.
- Microsegmentation: Networks are put into smaller zones to help stop breaches from spreading. Each section acts like a protective wall, so if one part is breached, it won’t take down the whole network. This setup also makes it easier to watch for and catch unusual activity quickly.
- Continuous monitoring: Trust isn’t permanent. It needs to be checked all the time. Using real-time data, organizations can spot and respond to unusual activity as it happens. Constant monitoring helps security stay up to date with new risks and vulnerabilities, providing strong, flexible protection.
- Secure access everywhere: Zero Trust works in any environment — cloud, on-premises, endpoints, containers, or hybrid setups. This means your critical resources are protected no matter where they are.
- Automate threat responses: Use automation to enforce security policies and contain breaches instantly. This speeds up your defenses, giving attackers less time to take advantage of weaknesses.
By following these principles, organizations can greatly strengthen their defenses against cyber threats while still working smoothly and efficiently.
The Evolution of Zero Trust
Why traditional security models fall short
The old way of securing networks focused on protecting the network perimeter. Once users, devices, or systems got inside the network, they’d have access to nearly everything. But with cloud computing, remote work, and smarter cyberattacks, the network perimeter doesn’t exist anymore. This means protecting the perimeter isn’t enough. Zero Trust was created to handle these new challenges.
The birth of Zero Trust frameworks
The Zero Trust model was created by John Kindervag in the 2010s while he worked at Forrester Research. Even after leaving Forrester, Kindervag continues to promote the Zero Trust model. Chase Cunningham took over developing and promoting Forrester’s Zero Trust frameworks starting in 2018.
Over time, the model has grown into a practical framework that helps IT and security teams build and use Zero Trust systems effectively.
Organizations like the U.S. National Institute of Standards and Technology (NIST) and the U.S. Department of Defense (DoD) have created detailed guides to help define and use Zero Trust. The NIST Zero Trust Framework and DoD Zero Trust Maturity Model act as step-by-step plans for businesses and government agencies.
How to build Zero Trust
Zero Trust needs a clear and organized plan:
- Define the Protect Surface: Identify what needs protection, understanding that the attack surface is constantly evolving.
- Map transaction flows: Gain visibility into communication and traffic flows to determine where security controls are necessary.
- Architect the Zero Trust environment: Once complete visibility is achieved, implement controls tailored for each Protect Surface.
- Create Zero Trust security policies: Develop granular rules allowing traffic access to resources within the Protect Surface.
- Monitor and maintain the network: Establish a feedback loop through telemetry, continuously improving security and building a resilient, anti-fragile system.
Tools and solutions for Zero Trust
- Zero Trust software: Tools like Illumio Zero Trust Segmentation use microsegmentation to help you create a strong Zero Trust strategy.
- Zero Trust in the cloud: Bring Zero Trust to the cloud with tools like Illumio CloudSecure and Illumio for Microsoft Azure Firewall.
- Zero Trust vendors: Pick cybersecurity platforms that support your Zero Trust strategy.
Microsegmentation
Microsegmentation puts networks into smaller, secure sections to prevent breaches from spreading. Illumio’s Zero Trust Segmentation uses this method to ensure that if an attacker gets into one part of the network, they’re stopped and can’t access other areas.
Positive impact for enterprises:
- Better data security: Keeping sensitive data safe is more important than ever with today’s cyber threats. Zero Trust makes sure only verified and authorized users can access data, greatly lowering the risk of breaches. By using microsegmentation and strict access controls, businesses can strengthen their defenses against threats from both inside and outside the network.
- Better Compliance: Mandates like GDPR, HIPAA, and CCPA require strict data protection. Zero Trust helps meet these requirements by closely controlling who can access data and what they can do. This reduces the risk of fines for breaking the rules and shows a strong focus on security best practices.
- Reduced breach impact: Breaches can happen, but Zero Trust helps keep them under control. If an attacker gets into one part of the network, they can’t move to other areas. This limits the damage, helps organizations recover faster, and reduces financial and reputation harm.
Zero Trust in action: Insights from Illumio
Illumio is a leader in Zero Trust, offering microsegmentation tools that transform how businesses protect their networks. Here's how we help you build a strong Zero Trust strategy:
- Policy-driven segmentation: Illumio makes it easy to create and enforce consistent, granular security rules for apps, users, and devices. This keeps each part of your network secure with custom protections, making it hard for attackers to move through the network.
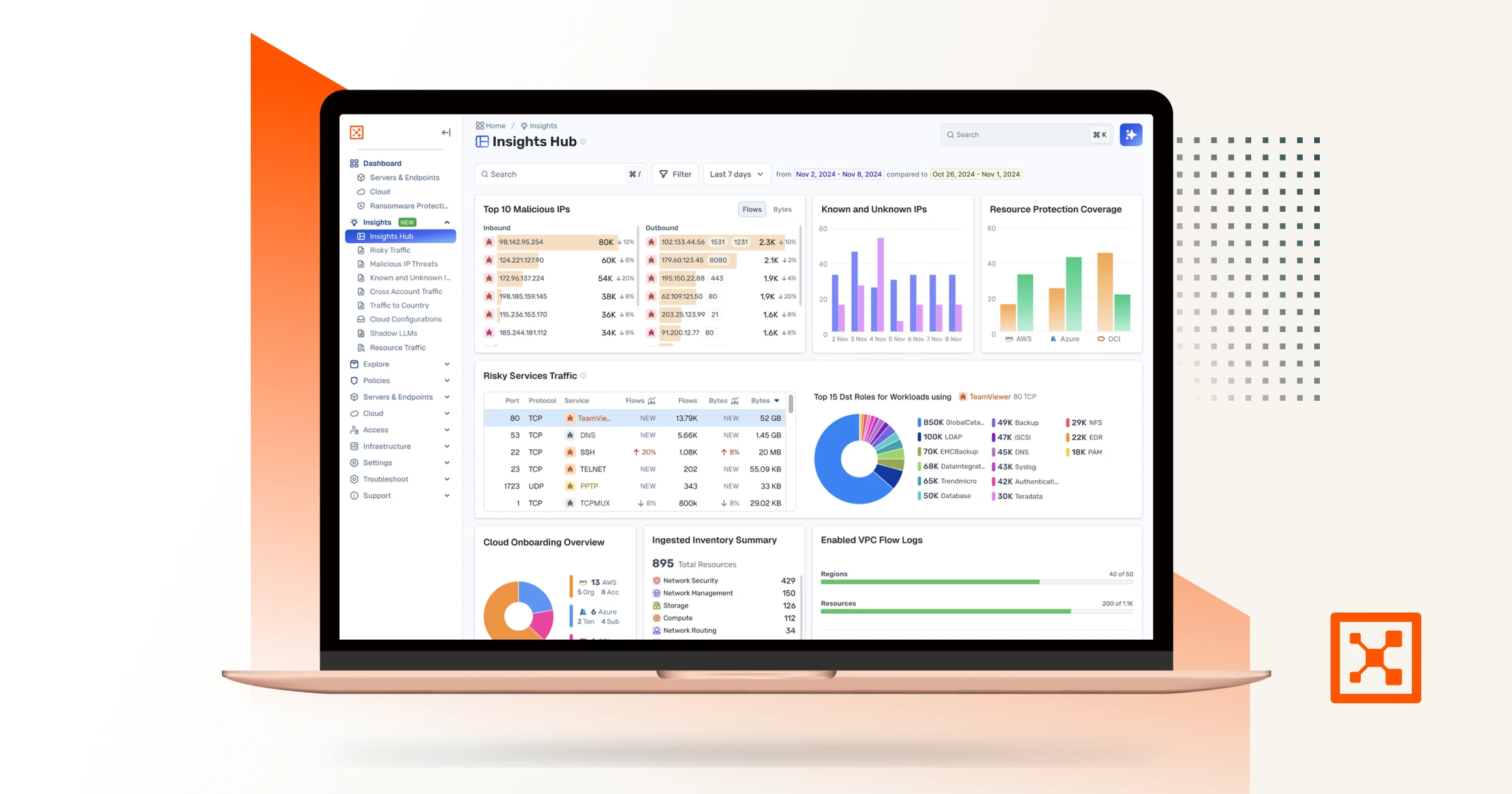
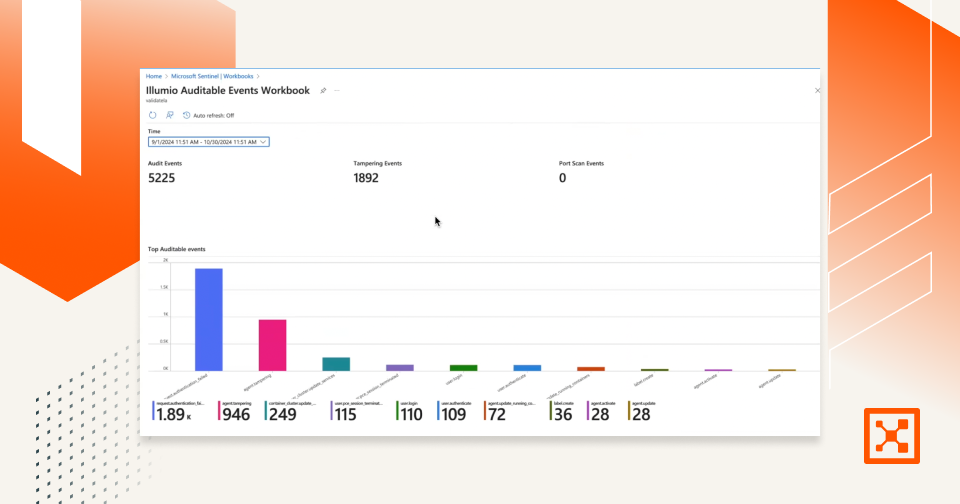
- Visibility into traffic: Illumio gives unmatched insight into how apps and workloads communicate in your network. This clear view helps IT teams spot unusual traffic or unauthorized access right away, cutting down response times to potential threats.
- Seamless integration: Illumio's solutions easily work with your existing IT setup, reducing disruptions. By connecting with current tools and systems, businesses can adopt Zero Trust without needing to completely rebuild their environment, making the switch smooth and simple.
- Reduced attack surface: Illumio Zero Trust Segmentation greatly reduces the attack surface. If one part of the network is breached, attackers are trapped in that area and can’t spread to other parts, keeping threats contained.
- Scalable security: Illumio's Zero Trust solutions grow with your business. Whether you're securing on-premises systems, cloud workloads, or a mix of both, Illumio provides reliable protection for everything.
With these tools, Illumio helps businesses strengthen their security and create a strong, proactive defense against constantly changing cyber threats.
Zero Trust Frequently Asked Questions (FAQs)
Question: 1. How is Zero Trust different from VPNs?
Answer: VPNs give secure access to a network, but Zero Trust secures each asset within the network individually.
Question: 2. What are the principles of Zero Trust?
Answer: Key principles include least-privilege access, microsegmentation, and continuous monitoring.
Question: 3. How does Illumio implement Zero Trust?
Answer: Illumio uses granular visibility and microsegmentation to enforce Zero Trust principles.
Question: 4. What is microsegmentation in Zero Trust?
Answer: It’s a Zero Trust tool that divides networks into smaller, isolated segments.
Question: 5. What are the benefits of Zero Trust for businesses?
Answer: Better security, less damage from breaches, and easier compliance with regulations.
Question: 7. How do I start implementing Zero Trust?
Answer: Start by assessing your security posture and using microsegmentation tools.
Question: 8. What is the NIST Zero Trust Framework?
Answer: It’s a set of guidelines for implementing Zero Trust in organizations.
Question: 9. Can Zero Trust work in the cloud?
Answer: Yes, Zero Trust cloud solutions provide robust protection for cloud workloads.
Question: 10. Who are the leading Zero Trust vendors?
Answer: Vendors like Illumio, Microsoft, and others lead the market with advanced solutions.
Conclusion
Zero Trust isn’t optional anymore in today’s connected and risky world — it’s a must-have. By using this advanced security model, businesses can leave behind old defenses and switch to a stronger, modern way to protect data, reduce breach impact, and meet regulations. Illumio’s expertise in Zero Trust Segmentation helps organizations shrink their attack surface, contain threats, and keep operations running smoothly.
Ready to strengthen your business’s security? Learn how Illumio’s Zero Trust solutions can transform your defenses by visiting Illumio’s Zero Trust page or reaching out for a custom consultation. Let’s improve your security together!
.png)


.webp)

.webp)