Around 76% of organizations experienced a ransomware attack in the last two years. Locking down the data center is not enough to completely reduce this risk.
Zero Trust Segmentation (ZTS) is crucial for any cyber resilience strategy to prevent ransomware or other breaches from spreading. Traditionally, segmentation has been applied to the physical network with a focus on the data center — but as some recent breaches have proven, the risk from ransomware is still looming.
The importance of extending a best practice from the data center to end-user devices is becoming critical.
Why extend segmentation to endpoints?
Endpoints are by many metrics the weakest link in an organization's security posture, partly because of the nature of endpoint devices but also because users are vulnerable to attacks. Knowing this, we shouldn't be surprised that IDC says that 70% of breaches start at the endpoint.
Hybrid work isn't disappearing anytime soon, and employees' laptops are exposed to a wide set of devices within networks not managed by IT. This results in an increased risk profile when one of these devices connects back into the corporate network.
But it doesn't stop with the increased unmanaged attack surface — endpoints are also more prone to security breaches due to:
- Phishing attacks: Threat actors using email to trick users into clicking on malicious links
- Social engineering: The art of tricking users into performing certain actions like sharing credentials
- Outdated software: Without proper patch management many users postpone updates
- Weak passwords: Users often use weak passwords that can be easily guessed or hacked, providing an easy entry point
By extending segmentation to endpoints, organizations can protect their assets by preventing any spread from the inevitably breached endpoint.
The best part? This provides proactive security without relying on detection, meaning that even with credential theft or a zero-day exploit, your high-value targets in the data center are still secured.
Quick ROI: Endpoint segmentation with Illumio
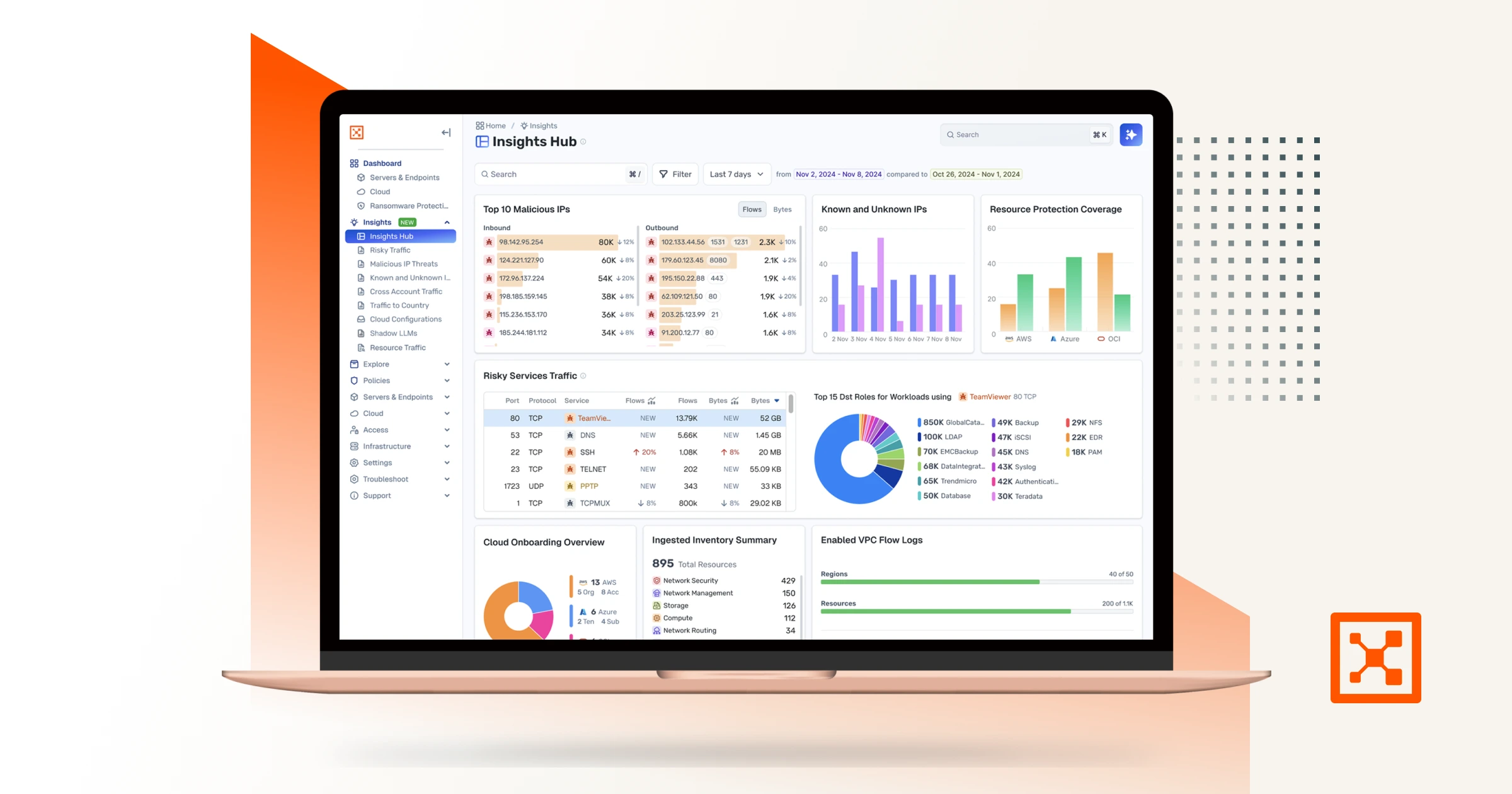
Illumio Endpoint provides ZTS for all workstations, laptops (including MacBooks), and VDIs from one single console.
By first providing visibility into all network traffic, including remote users, rule building is easy for a quick ROI that compliments existing EDR investments. With just a few simple rules, your security team can achieve quick wins by blocking all peer-to-peer connections between endpoints so ransomware can't spread. In case admins still need to RDP into these endpoints, exceptions can be made with a few more clicks.
By having all endpoint and server traffic visible in a single console, advanced rules can be created so only certain groups can access certain workloads (e.g., only Finance AD users can get access to the finance application).
Once you have visibility over all network traffic, not just in logs but in an interactive map, troubleshooting and rule building is a breeze.
With Illumio Endpoint you can:
- Visualize endpoint traffic anywhere: From home or the office, quickly assess and mitigate risk by seeing all network traffic
- Control application access: Don't expose endpoints to the data center — only allow defined users access to the right applications
- Secure endpoint exposure: Isolate cyberattacks to a single device — even before the attack is detected by other security tools

Enter the containment era with Illumio Endpoint
Endpoint security has long been in the detection era. By extending segmentation to endpoints, organizations can better protect against novel attacks, and in doing so, decrease the threat users pose to business-critical applications.
Embracing endpoint segmentation means you can move into the era of containment that's purpose built for forward-leaning security teams who have adopted an "assume breach" mindset.
Learn more about Illumio Endpoint here.
Contact us today to learn more about Illumio Endpoint with a free demo and consultation.


.webp)
%20(1).webp)