Zero Trust Security: The Ultimate Guide to Modern Cyber Defense
What is Zero Trust security?
Zero Trust security means no one gets automatic access ever. Not people, not devices, not apps. Everything has to prove who they are every time they try to connect, even if they’re already inside the network.
Traditional security assumes you can trust everything inside your system. But today, threats can come from anywhere, even inside your own walls. That’s why Zero Trust works on one core idea: “Never trust, always verify.” Let's learn about this essential strategy and how Illumio can help protect your organization from threats.
Why traditional security falls short
The legacy way of doing security — building walls around your network like a castle with a moat — just doesn’t work today. It was made for a time when everything lived in one place, like an office or a data center.
But now, work happens everywhere: in the cloud, at home, on the go. And cyberattacks have gotten way more advanced.
Key weaknesses of legacy security models:
- Too much trust inside the network. Once hackers get in, they can move around easily, stealing data or spreading ransomware.
- The perimeter is gone. People work from coffee shops, co-working spaces, and their homes. It’s tough to protect a boundary that doesn’t really exist anymore.
- Insiders can cause damage. Not all threats come from the outside. Sometimes it’s someone with real access doing harm — and old tools often miss it.
- Cloud makes things more complicated. Companies use tons of cloud apps and hybrid setups, which makes it harder to see and control who’s doing what.
- VPNs and firewalls slow things down. Routing all traffic through one spot can drag performance and leave you with a single point of failure.
- No real-time eyes on the network. Traditional tools check in every now and then. That’s not enough to catch fast-moving threats.
This is exactly why Zero Trust is the better way. It removes blind trust and checks every user, device, and request, no matter where it’s coming from.
The core principles of Zero Trust security
Zero Trust is built on a few key rules that help keep your systems safe, no matter where users are or what devices they’re using.
1. Always verify
You don’t just check someone once and let them in forever. Every user, device, and workload has to prove who they are over and over using things like multi-factor authentication (MFA), biometrics, and risk signals. The goal is to make sure whatever accesses the network is really who they say they are, every time.
2. Enforce least-privilege access
Even trusted users should only get access to what they need, nothing more. Zero Trust uses smart tools like role-based access to make sure no one has more power than they need. You can also give temporary access when needed and then take it away which helps stop attackers from gaining control.
3. Assume breach
Zero Trust doesn’t wait for an attack — it plans for one. That means watching for strange behavior, catching threats early, and making sure any damage is small. Real-time monitoring and AI tools help find and stop attacks before they get out of hand.
4. Microsegmentation
Microsegmentation breaks your network into smaller pieces. That way, if one area is hit, the attacker can’t move freely. Everything stays contained, and only approved connections are allowed between systems. Microsegmentation is foundational to any Zero Trust strategy.
5. Continuous monitoring and analytics
Zero Trust uses continuous monitoring to spot unusual activity. Machine learning helps understand what “normal” looks like, so anything weird stands out right away. That means faster threat detection and response.
6. Enforce Zero Trust policies across the network
It’s not just about your network. Zero Trust policies need to work across devices, users, apps, and cloud systems. Automated tools help apply the same smart rules everywhere, adjusting as threats change in real time.
Zero Trust security in action
Zero Trust cloud security
The cloud makes things complex — everything’s shared, and workloads are always changing. Zero Trust cloud security keeps each workload locked down and separate, no matter where it’s running. That means even in a busy, fast-moving cloud, your data stays safe.
How Zero Trust strengthens cloud security:
- Identity and Access Management (IAM): Every access request is authenticated and authorized.
- Workload segmentation: Prevents lateral movement between cloud applications.
- Encryption and secure communications: Ensures that all data transfers are encrypted end-to-end.
Zero Trust data security
Your data is your most valuable asset, and Zero Trust treats it that way. To keep it safe, you need strong protections like:
- Classify data: Tag and track your sensitive data so you know where it lives.
- Build strict access controls: Only the right people should have access — no more, no less.
- Automate encryption: Data gets encrypted whether it’s sitting still, being sent, or in use, so it’s always protected.
Zero Trust endpoint security
With more people working remotely, hackers are going after laptops and phones. Zero Trust endpoint security helps stop them by:
- Device posture checks: Ensuring only compliant devices can access resources.
- Behavioral monitoring: Detecting unusual activity on endpoints.
- Application whitelisting: Preventing unauthorized software execution.
Zero Trust security framework
A Zero Trust security framework provides a structured approach to implementation. This includes:
- Identity and access management (IAM)
- Microsegmentation
- Device security and compliance
- Real-time threat detection
How Illumio builds Zero Trust security
Illumio helps organizations lock down their environments with microsegmentation without slowing things down. As a top Zero Trust security company, Illumio gives you powerful tools to stop attacks before they spread — across data centers, clouds, containers, and endpoints.
Key Illumio Zero Trust security solutions:
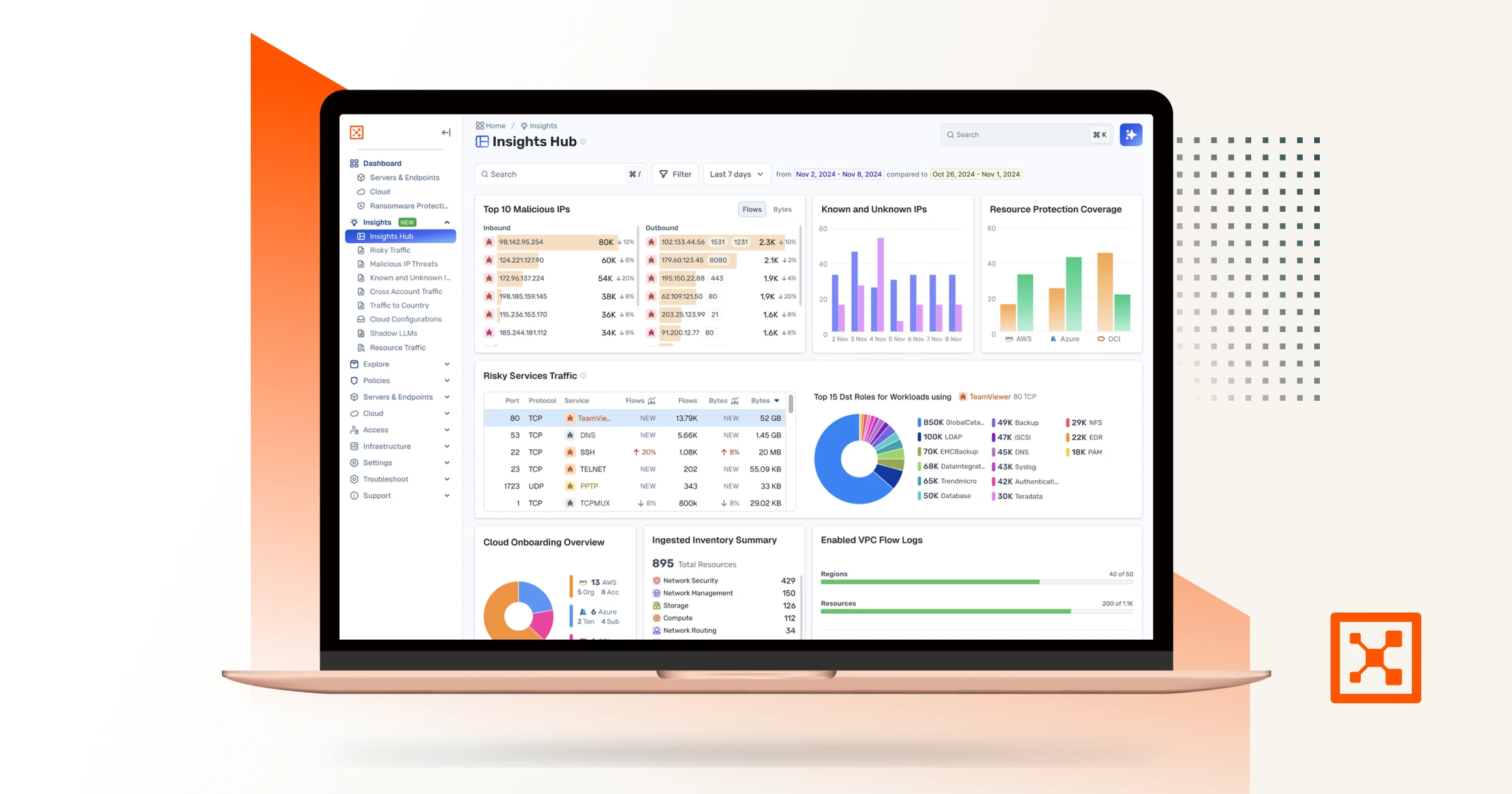
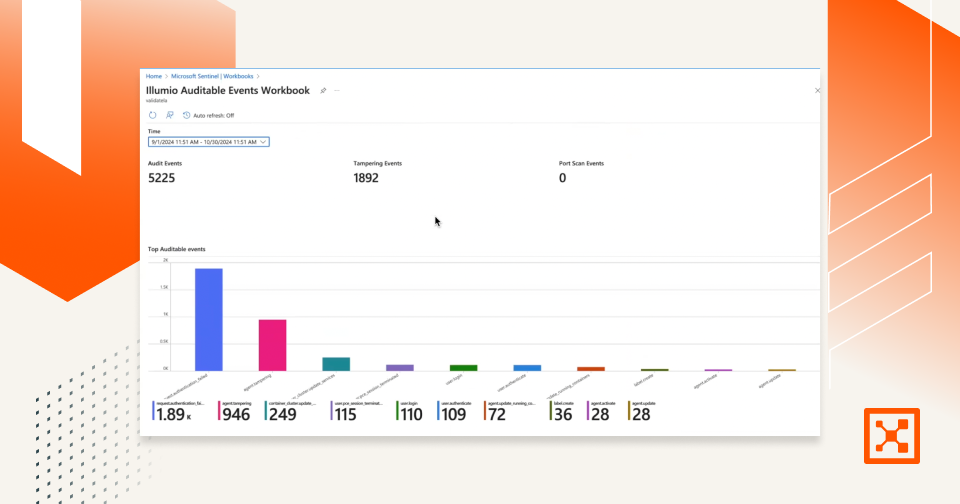
- Illumio Insights: Gives security teams the real-time context they need to see, prioritize, and act on risk faster.
- Illumio Segmentation: Stops the spread of attacks by isolating workloads across your hybrid, multi-cloud environment.
Container security with Illumio
Containers are great for scaling fast, but they’re tough to secure. Illumio makes it easier:
- Workload segmentation: Applies Zero Trust rules inside Kubernetes so only the right apps talk to each other.
- Dynamic policy enforcement: Updates security policies automatically as your containers change.
- Real-time visibility: Shows what’s happening inside your container traffic so you can stop threats early.
Positive impact for enterprise security teams
Using Illumio's Zero Trust security model delivers:
- Reduced attack surface: Microsegmentation and strict access controls limit the spread of threats.
- Faster incident response: Real-time visibility accelerates threat detection and mitigation efforts.
- Simplified compliance: Zero Trust helps meet regulatory requirements such as GDPR, HIPAA, and NIST, making audits easier and reducing compliance risks.
- Operational efficiency: Automating security policies minimizes manual intervention, allowing security teams to focus on higher-priority tasks.
Improved security posture: By adopting Illumio's Zero Trust solutions, organizations strengthen their cybersecurity resilience against evolving threats.
Zero Trust security frequently asked questions (FAQs)
Question: 1. How is Zero Trust different from traditional security models?
Traditional security models rely on perimeter defenses, while Zero Trust assumes no implicit trust and enforces strict access controls. zero trust assumes no implicit trust and enforces strict access controls.
Question: 2. Can Zero Trust security prevent ransomware attacks?
Answer: Yes, by implementing least-privilege access and microsegmentation, Zero Trust stops the spread of ransomware.
Question: 3. What industries benefit most from Zero Trust?
Answer: Financial services, healthcare, government, and any organization handling sensitive data benefit greatly.
Question: 4. Is Zero Trust security expensive to implement?
Answer: While initial deployment can be complex, the long-term cost savings from breach prevention make it a worthwhile investment.
Question: 5. How does Zero Trust protect remote workers?
Answer: Zero trust endpoint security ensures that remote devices comply with security policies before granting access.
Question: 6. What role does microsegmentation play in Zero Trust?
Answer: Microsegmentation isolates workloads, preventing lateral movement by attackers.
Question: 7. Can Zero Trust security be applied to cloud environments?
Answer: Yes, Zero Trust cloud security enforces strict access controls across cloud workloads.
Question: 8. How does Illumio enable Zero Trust security?
Answer: Illumio provides segmentation, endpoint security, and real-time visibility to enforce Zero Trust policies.
Question: 9. Does Zero Trust security impact user experience?
Answer: When implemented correctly, Zero Trust enhances security without causing significant disruptions.
Conclusion
Zero Trust helps organizations build stronger defenses that keep up with today’s fast-changing threats. Companies like Illumio are leading the way, making it easier and more powerful than ever to put Zero Trust into action.
.png)
.webp)
.webp)
%20(1).webp)

.webp)